AI-Powered Content Incident Response: Build a Crisis Triage Pipeline

Incidents are where messaging discipline gets tested for real. You’re balancing speed, accuracy, legal risk, and customer trust, all with a half-baked fact pattern changing by the minute. I’ve been in those threads. Everyone means well. Without a pipeline, you end up rewriting the same sentence seven times while Twitter turns your silence into a story.
Years ago, when I was running tiny teams, the only way we shipped content under pressure was to do the work ahead of time. Encode the voice. Freeze claim boundaries. Pre-approve the phrasing that won’t get Legal out of bed at 2 a.m. The day-of work dropped from writing to routing. That shift is the difference between steady updates and a credibility tax you’ll keep paying.
Key Takeaways:
- Speed without governance creates rework, retractions, and credibility loss
- Treat incident content like regulated copy: claim rules, safe phrasing, and provenance
- Routing and approvals are the bottleneck; writing is rarely the problem
- SLAs for content cut drift and reduce “hero moments” that don’t scale
- Encode claim safety and voice as rules so updates stay consistent across channels
- Use QA gates and atomic publishing to prevent conflicting updates and risky rollbacks
Why Ad-Hoc Crisis Content Breaks When It Matters
Ad‑hoc crisis content breaks because speed gets optimized and safety becomes an afterthought. Teams lean on prompts and intuition while facts are still forming, which pushes judgment onto rushed humans. A better approach encodes voice, claims, and channel rules upfront so the pipeline can produce safe drafts in minutes.

The Speed Trap With Ungoverned Prompts
Prompts feel fast when you’re staring at a blank field and your Slack is melting. But prompts don’t hold the system together. They push voice, claim safety, and accuracy checks onto people who are juggling 10 tabs and an exec ping. That’s how you get narrative drift, soft claims, and a legal review that starts with “where did this come from?”
What you’re really fighting is decision fatigue. Without ruled boundaries, every sentence is a fresh judgment call. You’ll see drafts bounce between PMM, Comms, Legal, and the on-call engineer while the situation evolves under their feet. You don’t need heroics. You need a governed default and a rollback plan that everyone trusts. Even a good writer turns into a blocker when the rules live in their head.
Speed does matter, but only when safety is solved earlier in the pipeline. Pre-approve what’s safe to say, what’s not, and how you describe severity and impact. Then the machine can write within those rules while humans focus on what changed, not how to phrase it.
For a sense of how teams are using AI on the intake side, see Resolver’s note on AI‑powered incident intake triage. The same logic applies to crisis content, with a tighter lens on claims and voice.
What Is Incident Content And Why Does It Differ From Regular Updates?
Incident content isn’t a blog post. It’s regulated copy under time pressure. You’re communicating risk, impact, and remediation while the situation is still moving. Docs, support macros, status pages, and social all carry different exposure and audiences, which means different templates, tone bounds, and publish targets.
Docs need context, steps, and timestamps. Support macros need empathy, clear next steps, and “don’t over‑promise” guardrails. Social needs brevity, alignment to the current state, and language that won’t get screen‑capped into a later discrepancy. The overlap is your single source of claim truth. Every channel pulls from the same state, defined once.
The mistake I see most often is treating all of this like a quick tweet. It isn’t. You’re writing with legal and customer retention in mind. That calls for minimal viable updates with traceable provenance, not creative flourishes. Templates aren’t about being robotic. They reduce the surface area for risk.
Why Most Teams Underestimate Claim Safety
Teams optimize for time‑to‑publish, not likelihood‑to‑retract. Claim safety feels like a “later” problem until the first correction thread eats an hour and a half. Move claim checks earlier. Define which product truths are frozen. Lock guarded terms. Pre‑approve legal‑safe phrasing for severity, impact, and remediation states.
You’ll also want a ruleset for when facts are unknowable. “We’re investigating,” “limited subset,” and “no evidence of X” all carry different implication weights. Write those once, get them signed off, and make them easy to slot into any draft. You shrink review cycles because reviewers are vetting risk, not rewriting words.
One more lens from security ops: AI can multiply triage speed, but only inside clear rules. Prophet Security talks about AI as a force multiplier for detection and triage in their post on AI as a force multiplier for incident triage. Content is no different. No rules, more risk.
Ready to cut retractions and keep your first update on‑message? See how teams run a governed flow with Oleno. Request A Demo.
Governance And Routing Are The Bottlenecks, Not Writing
Incident comms bottleneck at governance and routing because ownership is fuzzy and rules live in slides. You fix this by encoding a severity matrix, owners per level, and time‑boxed approvals per channel. Writing remains the smallest part of the work once the pipeline knows who decides what and when.

What Traditional Approaches Miss About Triage
Most teams chase a better draft. The failure is upstream. If the intake route, severity decision, and owner handoffs aren’t deterministic, every incident starts from zero. You need a severity matrix that’s actually used, not buried. You need SLAs that define time to first update and time to correction, per channel, by severity.
Routing is where minutes get lost. If the PMM on‑call isn’t obvious, your fastest writer becomes the slowest blocker. Make the on‑call roster visible, with backfills and a “can publish” permission that doesn’t rely on one person being awake. Add clear promotion and de‑escalation criteria so the pipeline adjusts channels and approvers as the situation changes.
Documentation helps, but systems win. Tie your triage rules to the content pipeline so classification triggers templates, reviewers, and publish targets. You’re collapsing the decision space under pressure by making the safe path the default.
For a deeper dive on automating elements of incident response, Dropzone’s guide on Automate incident response with AI maps well to how you should think about routing and SLAs in content too.
Who Approves What, And When?
Approval chains should vary by severity. For SEV‑1, PMM approves copy, Legal sanity‑checks claims, and Comms controls channel timing. For SEV‑3, PMM only. Put time‑bounds on each gate, five minutes for first pass, fifteen for publish, with an explicit rollback trigger if new facts conflict.
The practical win is predictability. Everyone knows their role, their timer, and the acceptable language. You’ll still need judgment calls, but those calls happen inside a system that keeps moving. I’ve seen teams cut decision time in half just by removing “who can ship this” from the equation.
You can bolt governance atop any workflow. Oleno bakes governance into execution so the rules apply automatically while the pipeline runs. That’s the piece most teams try to enforce in meetings and Slack threads. Meetings don’t scale under pressure.
The Hidden Costs Of Slow, Inconsistent Responses
Slow, inconsistent responses cost more than a few angry comments. Minutes compound. Edits multiply. Retracting a post trains your audience to wait for the second version. Track time to first update, correction rate, and how often channel states disagree. Those numbers tell the real story about risk and rework.
Minutes Matter When Narratives Spiral
Let’s pretend an outage hits at 9:02. No statement until 9:28. Screenshots circulate. Your first message underplays impact, then you edit it at 9:41 and again at 10:05. Each extra 10 minutes compounds confusion and creates more support tickets. The fix is boring: a governed default and a timer you can hit.
Measure mean time to first update by severity. Track edits per post and reasons for change. If your corrections skew toward claim safety, move those checks earlier. If they skew toward state alignment, you have a routing problem. I tend to start with a baseline target, then tighten once the system is stable.
Engineering Hours Lost To Redo And Legal Escalations
Rushed drafts trigger three‑way Slack threads, legal edits, and doc rewrites. Assume three people times forty‑five minutes per incident times six incidents per quarter. That’s 13.5 hours of senior time, plus the frustration tax. Multiply by a couple of misaligned channel states, and your week vanishes.
Automate provenance and claim checks so review focuses on risk, not hunting for invented facts. Grounding outputs in approved sources reduces the back‑and‑forth by removing “where did this come from” as a question. Radiant Security’s write‑up on how AI‑enabled incident triage works shows a similar pattern in ops: shrink the surface area for human review to the actual judgment calls.
Stop chasing approvals across five channels. Start shipping governed updates on a clock with Oleno. Request A Demo.
The Moments That Break Trust, And How To Avoid Them
Trust breaks when channels disagree or language overpromises. Prevent this by anchoring every update to a single source of claim truth, templating high‑risk phrases, and publishing atomically across channels. If you must revise, roll back everywhere in one move so no one sees two realities.
When Your Biggest Customer Sees Conflicting Updates
Docs say degraded. Status page says resolved. Social says investigating. That’s how a small incident becomes a credibility problem with your largest account. Build a central state object for the incident, then force channel outputs to reference the same state and timestamp. One truth, multiple formats.
If you need to revise, do it atomically. Update docs, macros, and social together, or none of them. Publish notes should reflect the same reason for change across channels. You can’t stop screenshots, but you can make the narrative consistent. That alone cuts a surprising amount of “what’s really happening” noise.
The Three Channels That Create Whiplash
Docs, support macros, and social create the most whiplash because they reach different audiences at different clock speeds. Give each a minimal viable template and a safe language list. Lock verbs for severity descriptions. You’re not trying to sound robotic. You’re making sure “degraded” doesn’t mean three different things in one hour.
Leadership often underestimates how fast contradictions spread. Once they do, the next update has to work twice as hard. There’s decent research on rapid triage and team coordination under pressure. One useful overview is in PMC11575424’s triage research. The lesson carries over: clarity and cadence beat ad‑hoc cleverness.
Build A Governed Crisis Triage Pipeline That Scales
A scalable crisis pipeline encodes severity, owners, SLAs, and claim rules so the safe path is the default. Classification triggers templates, reviewers, and publish targets. Provenance is required, and rollback rules are explicit. Humans make judgment calls. The system runs the rest on a clock.
Classify Incidents And Define SLAs
Start with a five‑level severity model, owners per level, and time‑to‑publish targets per channel. Example: SEV‑1, PMM lead, Legal reviewer, Comms publisher, first update in ten minutes, refresh every thirty. Encode rules so classification auto‑selects templates and reviewers. Promotion criteria should add channels and approvals, not invent new ones mid‑stream.
Tie SLAs to alerts the pipeline sends, not reminders people have to set. If an approval times out, escalate to the backfill or auto‑publish a minimal viable update with safe phrasing, then schedule the next refresh. You’re designing for reliability, not heroics. That’s how the cadence holds when people get pulled into other work.
Governance Checklist And Legal‑Safe Phrasing Templates
Codify allowed claims, prohibited phrases, and product truths. Build short‑form templates for social and macro replies, long‑form for docs. Add a pre‑publish checklist: voice rules applied, grounding present, citation included, claim category selected, timestamp verified. Convert common legal edits into reusable snippets you can slot in fast.
You can move a lot of friction out of the timeline with these rules. Reviewers spend their time on “is this risky” instead of “say it like this.” Over time, those snippets become a library that makes the first draft safer and the second draft unnecessary more often than not.
How Oleno Implements Governed Incident Response End To End
Oleno runs this playbook by starting with governance and enforcing it at every step of the pipeline. You define voice, claim boundaries, product truth, and channel rules once. Oleno applies them automatically as content moves from draft to QA to publish, with idempotent pushes and atomic rollbacks to keep channels aligned.
Governance As Code For Claims And Voice
Oleno begins with governance, not output. You encode voice patterns, phrasing rules, approved claims, and product facts so generation stays inside boundaries even when the clock is tight. Those rules apply to every draft in every studio. Result, fewer legal escalations and less frustrating rework when you can least afford it.

Because governance is system‑level, the narrative doesn’t drift as volume increases. Oleno keeps opinionated structure intact while letting you tune specifics per channel. You’re not trusting memory. You’re relying on rules the engine enforces consistently.
Pre‑Publish QA Gates And Fast Approvals
Nothing ships in Oleno until it passes QA checks for voice alignment, narrative structure, clarity, repetition, grounding, and LLM‑readability. Approvers get a compact diff with failures called out, provenance attached, and linter results ready. Approve in minutes, not threads. If a check fails, Oleno remediates based on your rules, then re‑tests before you can publish.
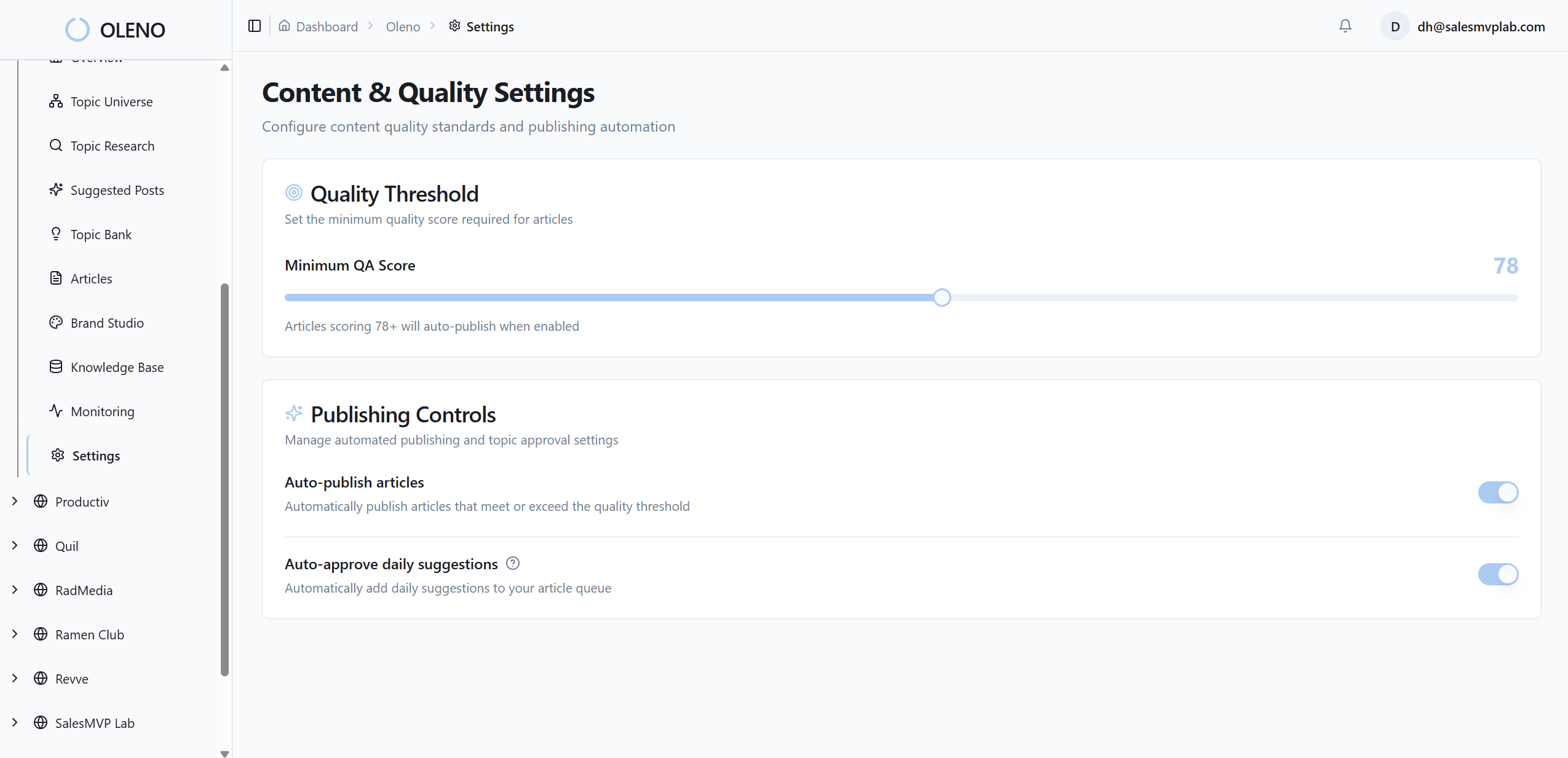
Tie approvals to your severity model. SEV‑1 can require Legal, SEV‑3 can be PMM‑only. Oleno enforces the path you configure so people aren’t debating process while customers are waiting. That alone cuts the hidden cost you felt earlier, where routing, not writing, was the bottleneck.
CMS Publishing, Multichannel Sync, And Safe Rollback
Oleno publishes directly to your CMS stack, including WordPress, Webflow, HubSpot, and more. Publishing is idempotent to avoid duplicates, and updates are handled atomically so docs, macros, and social stay in lockstep. Channel‑specific formatting is supported without inventing new claims, which reduces “two realities” in the wild.
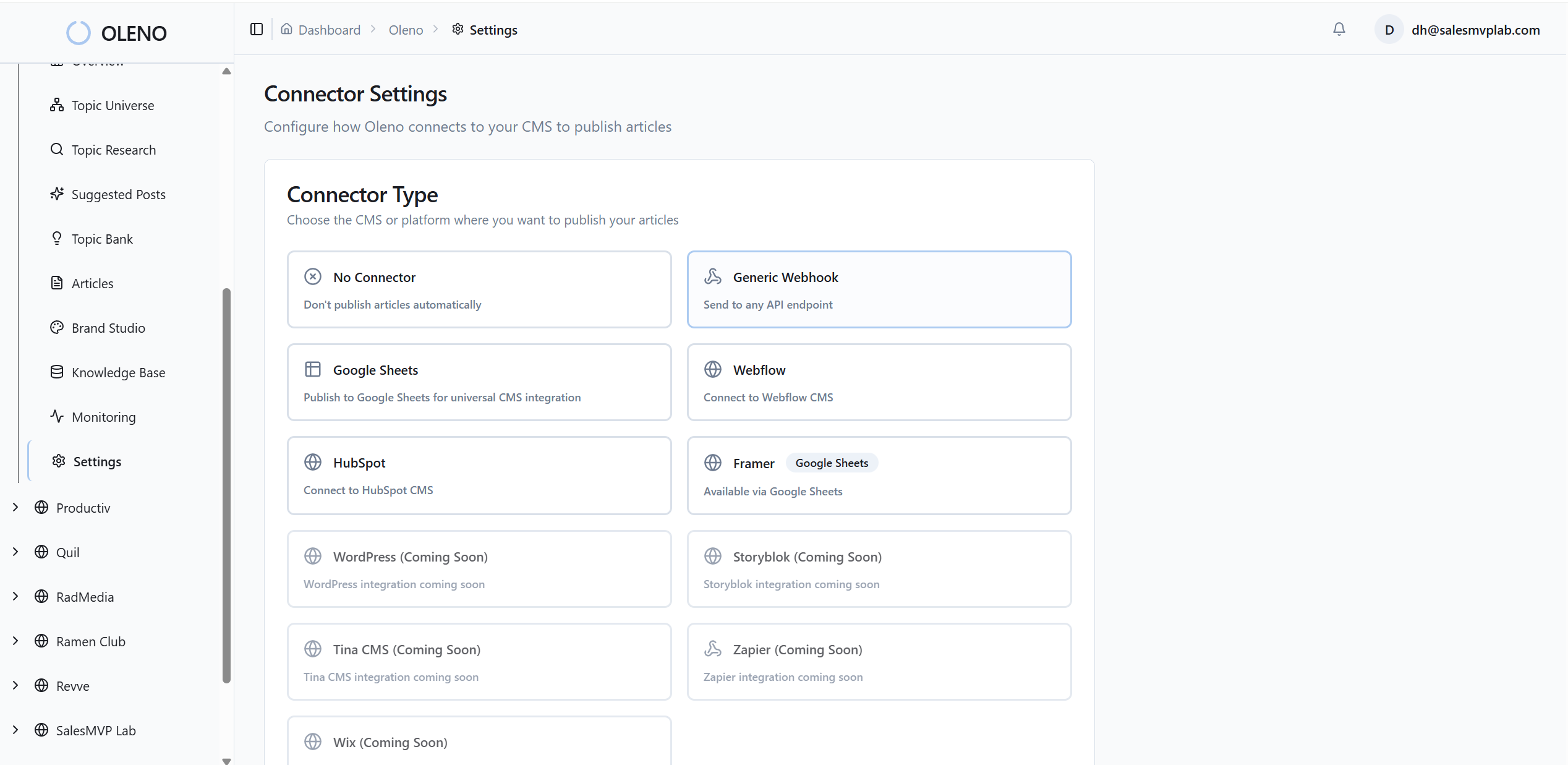
When a correction is required, Oleno executes rollbacks safely and synchronizes updated copy across channels in one action. Audit logs capture what changed and why. Reviewers don’t have to hunt, and your audience doesn’t have to reconcile conflicting messages. You keep trust intact while the facts settle.
Oleno is designed to be the execution layer that small teams can depend on during their worst hours. Ready to let the system handle the mechanics while you focus on judgment? Request A Demo.
Conclusion
Crisis content doesn’t fail because people don’t care. It fails because the system asks them to decide everything while the clock is running. Encode claims and voice. Define owners and SLAs. Ground every sentence in real sources. Then let the pipeline do its job. That’s how you publish fast, avoid legal drift, and keep trust when it matters most.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions