Compliance‑Safe Programmatic SEO: Prevent Legal Risk While Scaling Content

Programmatic SEO at scale can be an asset or a liability. The difference isn’t how fast you can ship pages. It’s whether your system prevents risky claims from ever getting near publish. When pace goes up and guardrails are weak, cleanups multiply, legal gets jumpy, and your team becomes a manual review department. Nobody wants that job.
I’ve seen both sides. At one company, we recorded founder videos and transcribed them into posts. Fast, scrappy, and… structurally fragile. Great ideas, poor scaffolding. Later, with a high-volume contributor network, we hit real traffic scale, but only because we paired volume with rules and structure. Same lesson, over and over: speed is fine; speed without constraints is a mess.
Key Takeaways:
- Guardrails must live in templates and pipelines, not in people’s heads
- Encode banned terms, disclosure requirements, and numeric bounds as policy, not advice
- Set QA-as-code gates that block publish when rules fail and route edge cases to humans
- Ground claims in an internal knowledge base so provenance is traceable
- Use idempotent publishing and audit trails to cut cleanup time when issues occur
- Compliance and cadence can coexist when rules apply upstream, automatically
Why Scale Without Guardrails Becomes Liability, Not Leverage
Scaling programmatic pages creates risk when claims aren’t constrained by rules, templates lack required evidence, and disclosures are inconsistent. The problem isn’t volume; it’s ungoverned generation. Move risk points into the pipeline, template schema, data joins, and metadata, and bind them to policy. When compliance is structural, speed stops being scary.

What Actually Creates Legal Risk In Programmatic Pages?
Legal risk creeps in through uncontrolled statements, implied promises, missing disclosures, and ambiguous phrasing that reads like advice without proof. It’s rarely one sentence. It’s usually the combination of a speculative claim, a thin template, and no evidence field. Once that hits production, you’ve shipped a liability at scale.
You fix this by mapping where risk enters the system: templates (what’s required), data joins (what’s allowed), and metadata (what’s disclosed). Then you turn each into a rule the pipeline can evaluate. It’s not glamorous work. It is the work that keeps your brand out of trouble and your team out of rework hell.
If you want a deeper primer on compliance patterns for programmatic builds, this overview of a programmatic SEO compliance and quality framework is a solid reference.
The Myth That Compliance Kills Speed
Compliance gets cast as the blocker. That’s not the full story. What actually slows teams down is manual compliance, late-stage reviews, subjective edits, and “can someone sanity-check this?” threads. When rules live upstream and apply automatically, review time shrinks. Cadence stabilizes. Fewer fires, fewer reverts, fewer 11pm decisions.
Here’s the shift: stop enforcing standards with meetings. Enforce them with code. If templates can’t render without required disclosures and the QA gate blocks risky claims, legal gets involved only on exceptions. You’ll still need human judgment. You’ll just save it for the places it matters.
Where Thin Templates Invite Unsupported Claims
Thin templates invite speculation because they create gaps models try to fill. That’s where risky language slips in, superlatives, promises, comparative claims, and numerical assertions without a source. The fix is structural: require citations, constrain numerics with ranges and units, and define permitted phrasing blocks for sensitive topics.
Make certain fields mandatory. Tie claim blocks to evidence fields. Bake disclosures into schema, not copy. And set hard publish stops: no citation, no publish. Safety becomes structure, not a last-minute edit. It’s quieter. Your editors will thank you.
Want to see a rules-first pipeline in practice? When you’re ready, Try Oleno For Free.
The Real Root Causes Of Compliance Failure In Automated Pages
Compliance fails when claim rules live in memory, regulated terms aren’t mapped to policy, and prompts drift over time. Most playbooks optimize for CTR, not claim safety. The fix is explicit: codify forbidden terms, required disclosures, numeric bounds, and exceptions in machine-readable rules, then let your pipeline enforce them.

What Traditional Playbooks Miss About Claim Control
Traditional content playbooks focus on keywords, headlines, and conversion elements. Necessary, but incomplete. They rarely encode forbidden claims, regulated terms, or disclosure logic. Instead, they depend on good intentions and careful editors. That works at 10 pages. It falls apart at 1,000.
Move this knowledge out of heads and into a ruleset your system can read: banned lists, context-aware allowlists, and “disclosure required” flags tied to content types. If your template can’t render a comparison block without a qualifier, you’ve already prevented the most common mistakes.
The Hidden Complexity Across Regulated Terms And Disclosures
Words like “recommended,” “guaranteed,” “safe,” or “best” aren’t neutral in many markets. Add region-specific disclosures, competitor references, and industry guidance, and complexity jumps. Manual memory fails under that load. Systems don’t. Build a canonical map of risk terms, disclosure snippets, and jurisdictional exceptions your pipeline consults every time.
This is where many teams underestimate the setup. It’s upfront work. But once encoded, you remove guesswork from the baseline and reserve human attention for genuine edge cases. If you want more patterns here, this walkthrough on safe programmatic SEO at scale is helpful.
Why Prompts And Manual Reviews Will Never Scale
Prompts drift. People get busy. Review queues pile up. As volume rises, humans become both bottleneck and safety net. That’s fragile. Replace memory with machine-readable rules and replace one-off prompts with deterministic structure. You’ll still use human judgment, just at the right altitude.
I’ve been in rooms where a great writer drafted faster than the team could review. Impressive output, inconsistent guardrails. The editing debt erased the speed advantage. You don’t win by typing faster. You win by making fewer things require late-stage judgment in the first place.
The Costs You See, And The Ones You Pay Later
The obvious cost is legal cleanup. The hidden costs are engineering toil, republishing work, reindex delays, and search trust erosion from weak evidence. A single risky pattern replicated across thousands of pages creates weeks of rework. Preventing that pattern at the template level takes an afternoon.
Let’s Pretend A Thousand Pages Slip A Risky Claim
Let’s pretend 1,000 local pages assert “guaranteed savings” without evidence. Even at five minutes to locate, edit, republish, and reindex each one, you’re looking at 83 hours. That’s two full-time weeks burned on cleanup. And that ignores brand damage, lost trust, and all the new content you didn’t ship.
I’ve watched this movie. At one company, we shipped fast and fixed later. The team paid in nights and weekends. Worse, it trained people to avoid shipping. Momentum died. It’s not about being perfect. It’s about not creating the same avoidable problem at scale.
Engineering Hours Lost To Cleanup And Rollbacks
Bad outputs break pipelines. Rollbacks, redirects, and republishing create hidden toil, dev tickets, queue retries, cache invalidation, QA cycles. Multiply publish failures by retries and you get a backlog that crowds real work. This is why idempotent publishing and clear rollback paths aren’t “nice to haves.” They’re cost control.
With idempotent writes, a retry won’t duplicate or drift content. With versioned publishes, rollback is a switch, not a project. Engineering gets their weekends back, and marketing keeps cadence instead of pausing for a site-wide triage.
When Thin Citations Erode E‑E‑A‑T And Rankings
Search now favors verifiable expertise. If pages lack sources, author context, and provenance, algorithms treat them as low value. You can fix this at the template layer. Require citations, bios, and evidence fields. Make trust a default, not an extra. Google’s guidance on using AI‑generated content responsibly points in the same direction: quality and accountability signals matter.
The win isn’t just “rank better.” It’s “avoid volatility.” Evidence-backed templates are more resilient to updates because they reflect real-world expertise signals, not copy that merely sounds confident.
Still managing this with ad-hoc fixes? It might be time to reduce manual QA load. Try Generating 3 Free Test Articles Now and see how upstream rules change the workload.
The 3am Moment No One Wants
Regulator notes in legal’s inbox, a viral screenshot of a misleading table, or a competitor calling out a risky claim, these moments don’t care about your sprint plan. The only real defense is evidence and process, rules, audit metadata, and the ability to show exactly what shipped and why within minutes.
When A Regulator Email Lands In Legal’s Inbox
There’s one response that keeps the room calm: receipts. Show the template, the rule that allowed the claim, the source that supported it, and the exact version that shipped. If you can produce that in minutes, you change the tone from panic to process. You’re not debating. You’re demonstrating.
To do this, you need provenance to travel with the draft and into publish metadata, policy versions, model settings, evidence references, reviewer IDs. If your system captures that automatically, you can answer hard questions without assembling a task force.
How A Single Tweet Triggers Brand Damage
One screenshot of a misleading comparison table travels fast. You can’t delete it from the internet. But you can reduce the odds by blocking tables that fall outside numeric bounds, requiring sources under every chart, and gating comparative language through approved phrasing. Small constraints. Big messes avoided.
We’ve all seen the “well-meaning chart” that implied a promise the product never made. That’s a template issue, not a copy issue. Lock the structure. Force the evidence. Limit the adjectives. Your comms team will sleep better.
What Would Have Prevented This?
Usually three things do the trick. First, a forbidden-claims list tied to a linter that blocks superlatives and promises without qualifiers. Second, a citation-required rule for sensitive statements. Third, soft-fail staging that routes flagged drafts to human review. You keep shipping the low-risk majority while high-risk pages wait for inspection.
If you want patterns beyond basics, a brief on programmatic SEO best practices covers structural safeguards that reinforce reliability as volume increases.
Build A Compliance‑First Programmatic Pipeline That Still Ships
A compliance-first pipeline encodes risk as rules, requires evidence in templates, and gates publishing with QA-as-code. It grounds claims in your internal knowledge and escalates only true edge cases to humans. The result: speed and safety in the same system.
Map Risks Into Rules, Not Checklists
Start with an inventory: regulated terms, forbidden claims, jurisdiction-specific disclosures, risky verbs, numeric ranges, and context rules. Encode them as machine-readable policies, banned lists, allowlists, disclosure flags, and range constraints. Then attach those policies to template schema and QA checks so enforcement happens by default.
You’re moving from “remember to” to “impossible to forget.” Don’t rely on training to prevent drift. Teach the system what “unsafe” looks like and make it impossible to render risky sections without required context. People still make judgment calls, just far fewer of them.
Design Claim‑Safe Templates That Still Satisfy Search Intent
Add mandatory fields for citations, author context, disclosures, and data provenance. Define permitted language blocks for comparisons and sensitive categories (health, finance, legal-adjacent). Use structured sections that answer intent upfront and tie each claim block to an evidence field.
The goal isn’t to write like a lawyer. It’s to make claims easy to verify and hard to misread. Templates should anticipate the most common errors, superlatives, unbounded numerics, implied guarantees, and block them before a draft exists.
Implement QA‑As‑Code Checks That Gate Publishing
Create declarative checks that run automatically: “no claim without citation,” “numeric values must include units and acceptable ranges,” “no superlatives without qualifiers.” Wire those checks to a publish gate. Failing pages stay in draft. Low-risk outputs pass seamlessly. Edge cases get routed to review.
This reduces the editorial pile-up. Reviewers aren’t proofreading for consistency; they’re adjudicating true exceptions. It’s a better use of human time and a cleaner path to consistent output.
Ground Every Claim With KB‑Backed Provenance
Point generation at an internal knowledge base that contains product truth, policies, and approved claims. Require inline citations that resolve to specific passages. Store evidence metadata on each record so a sentence can be traced back to its source.
You’re not just “adding sources.” You’re making accuracy repeatable. When the market changes or policies update, you revise the KB and reflow evidence across templates without rewriting every page.
Set Human Escalation For Edge Cases
Define triage thresholds. Any use of a regulated term in a title? Comparative claims involving competitors? Financial or health guidance? Those trigger soft-fail staging. Assign review to legal or a subject matter expert with a clear SLA, and capture decisions in the audit log. Exceptions get attention; routine content ships.
This is how you respect risk without slowing the entire program to a crawl. The default is publish. The exceptions are escalated. Everyone knows which is which.
Add Publishing Controls And Immutable Audit Trails
Adopt idempotent publishing so retries don’t duplicate or drift content. Version each publish with policy snapshots, model settings, evidence hashes, and reviewer IDs when used. Enable rollback through a single version switch. When questions arise, you can see exactly what shipped and why.
For a broader strategy view on compliance patterns, this practical take on programmatic SEO compliance and quality outlines how teams embed guardrails upstream and sustain throughput.
How Oleno Operationalizes Compliance From Draft To Publish
Compliance at scale requires governance rules, knowledge grounding, QA-as-code, and publishing controls that don’t rely on heroics. Oleno encodes those pieces so small teams can ship continuously without creating rework. Strategy stays human. Execution becomes a system.
Governance Rules And Claim Boundaries Applied Everywhere
You define product truth, approved claims, banned terms, and voice rules once. Oleno applies them across briefs, drafts, and final assets. Policy isn’t a slide deck; it’s a constraint the engine respects at every step. Nothing publishes until outputs align with your rules, which reduces review burden and keeps language inside permitted boundaries.
This is particularly important for comparative content, regulated phrasing, and numerical assertions. Rules flow into template schema and draft generation, not just a final pass. Fewer surprises. Fewer late-stage edits.
Knowledge Base Grounding And Provenance Citations
Oleno grounds content in your internal knowledge base so facts stay aligned to reality. A KB-backed citation layer attaches sources to sensitive statements, and evidence travels with the draft, then the page. When you need to “show your work,” you can trace each claim to a specific proof point without assembling a committee.

This is how you avoid the 83-hour cleanup scenario. You update the KB once, then regenerate or refresh outputs with correct references, faster than chasing text across thousands of URLs.
Automated QA Gate And Policy Checks Before Publish
Oleno runs a QA gate with narrative, accuracy, and safety checks tied to your governance. Policies like “citation required,” numeric boundaries, and forbidden claims block publish until resolved. Low-risk pages pass automatically. Risky ones move to a human queue with context. The net effect is fewer incidents and a steadier cadence at volume.
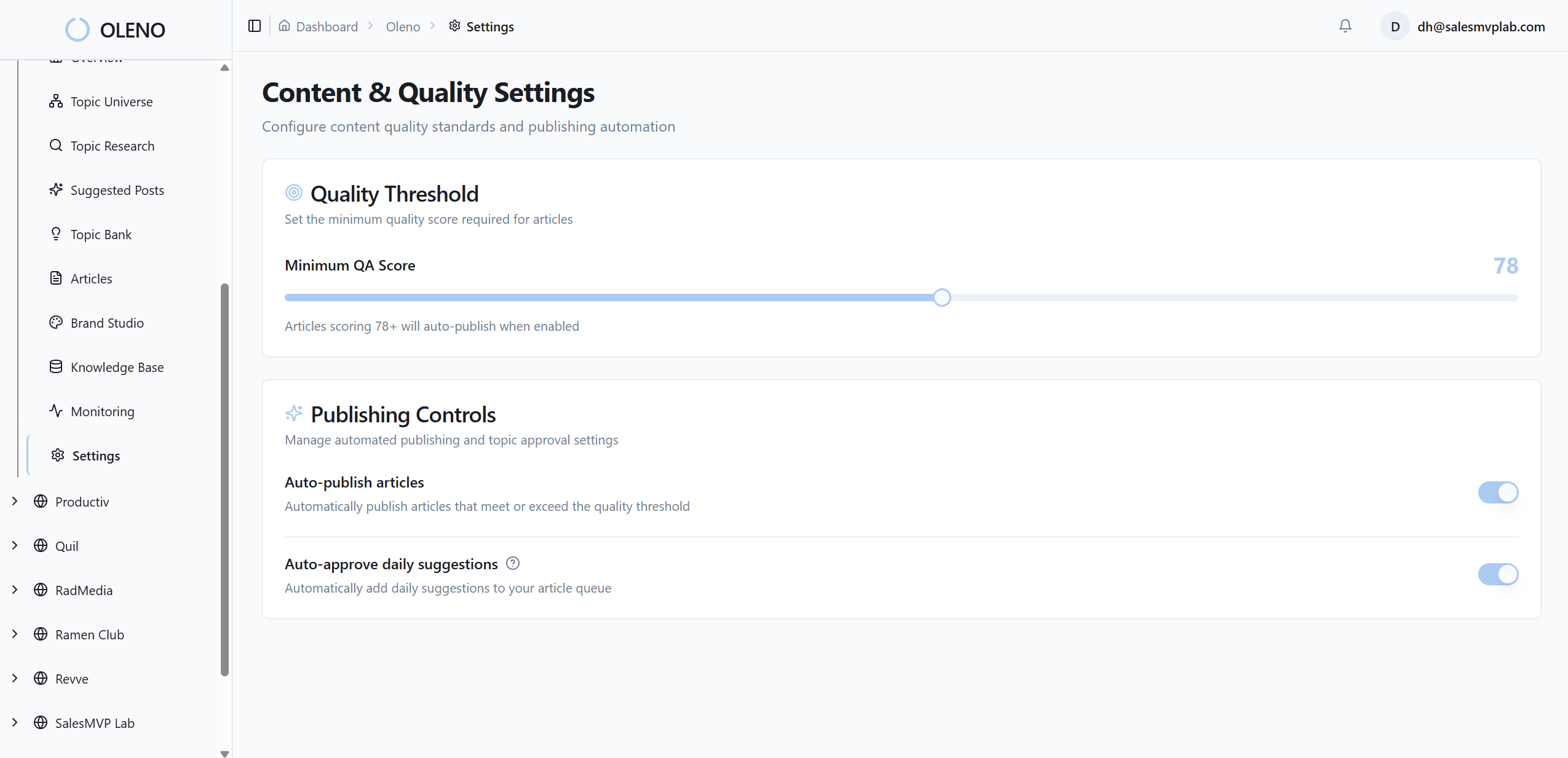
This directly addresses the costs we covered: less manual review debt, fewer rollbacks, and a lower chance of shipping risky language that requires wide-scale rework.
CMS Publishing, Idempotency, And Audit Metadata
Oleno publishes to your CMS as draft or live with idempotent writes, so retries don’t create duplicates. Each publish is stamped with audit metadata, policy versions, KB references, and reviewer IDs when applicable. If you need to rollback, you flip versions. If someone asks “who approved this,” the answer is in the record.
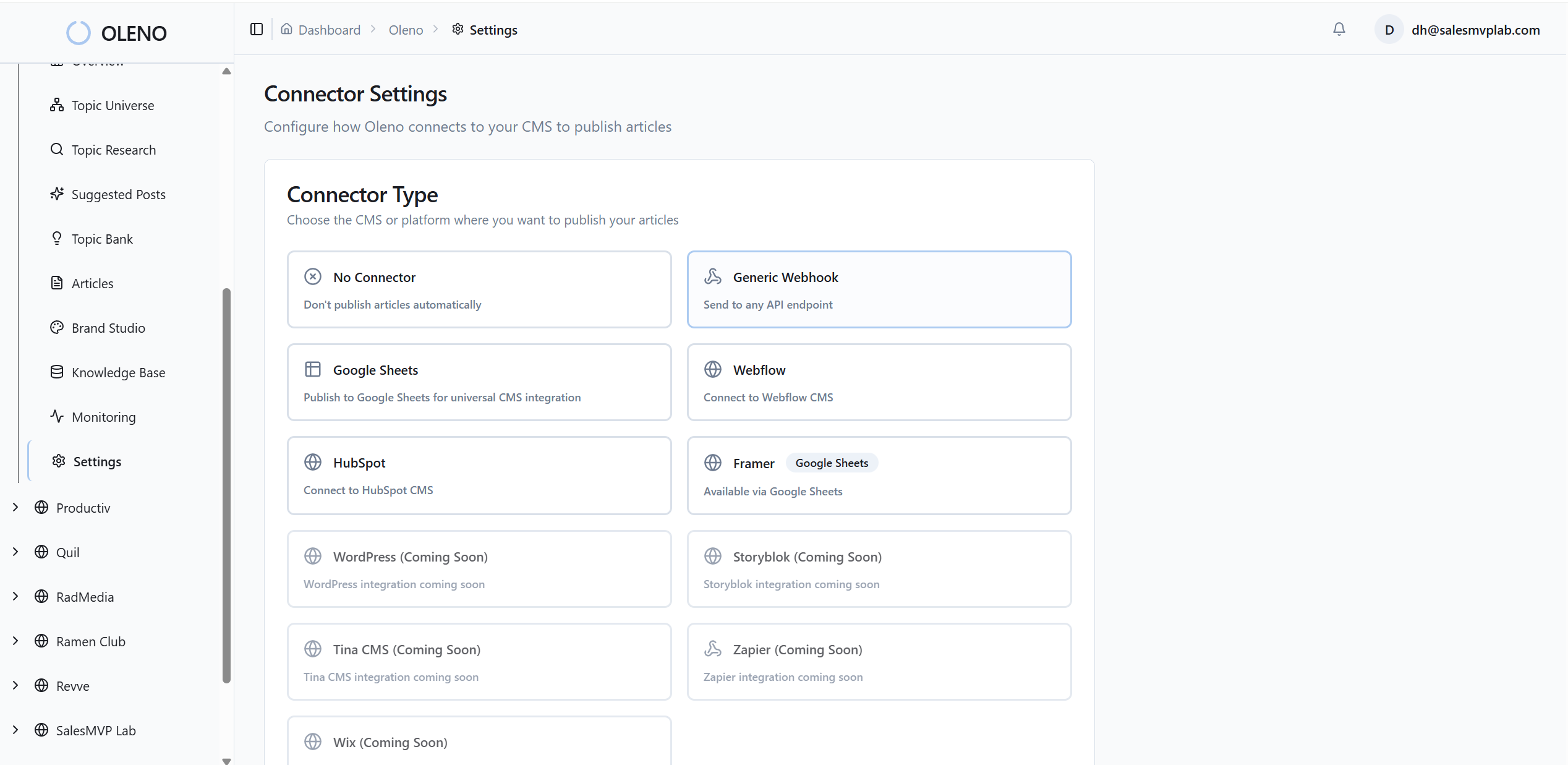
Oleno isn’t promising perfection. It’s giving your small team the operational layer to run programmatic SEO safely: rules at the front, QA at the gate, provenance in the record, and control at publish. That’s how you scale without inheriting a cleanup backlog.
Ready to operationalize this approach without adding headcount? Try Using An Autonomous Content Engine For Always‑On Publishing. Prefer to start small? Try Oleno For Free and generate a few test articles with governance turned on.
Conclusion
You don’t need more prompts. You need a system. Put rules upstream. Bind claims to evidence. Gate publishing with QA-as-code. Keep humans for judgment, not memory. When compliance becomes structure, you stop choosing between speed and safety. You scale output, reduce rework, and sleep through the night, no 3am surprises.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions