Multichannel Content Governance: Enforce Voice & Claims Across Channels

Most teams have a solid style guide and a shared sense of "how we sound." And then the work hits the real world, web templates, social schedulers, email builders, app release notes, and it all drifts. Not because people don't care. Because rules live in slides while content gets assembled in channels.
I’ve been on both sides. The founder who posts a spicy claim on LinkedIn. The marketer who then gets the "can we actually say that?" Slack. The fix isn’t more meetings or stricter copy notes. It’s pushing governance into where the work actually happens, fields, templates, and gates that enforce truth and tone before anything goes live.
Key Takeaways:
- Push governance rules into templates, schemas, and linters or they won’t survive channel translation
- Build a governance-to-channel matrix that maps policies and claims to specific fields and templates
- Enforce voice with tokens (cadence, banned phrases, CTA verbs) and verify claims with KB-backed citations
- Quantify rework and risk to unlock budget for pre-publish controls and policy-as-code
- Runbooks, owners, and SLAs make speed and safety compatible, especially on Fridays
- Use deterministic pipelines and QA gates; reviews handle exceptions, not the system
Governance Alone Will Not Survive Channel Translation
Governance only works when rules live where content gets built and published. Style PDFs don’t block risky claims or enforce CTAs inside a channel’s constraints. For example, a Twitter character limit or a CMS’s default alt text will override your intentions unless the template validates the rule.

The style guide myth that creates drift
Style guides are necessary, just not sufficient. They codify who you are; they don’t enforce how you show up in a Facebook placement with truncated headlines or an email client that strips inline CSS. Drift starts where rules meet templates and channel quirks. If you’ve ever watched a beautiful headline get cut mid-sentence in a mobile card, you’ve seen it.
The fix is structural, not motivational. Put the rules where content is assembled. If the ad template requires a CTA verb from an approved list, writers don’t have to remember it. If the docs generator fails builds when a risky claim is missing a citation, you don’t need a legal review at the eleventh hour. That’s the shift, from taste to tests.
What is a governance to channel matrix?
A governance-to-channel matrix maps policies and claims to the exact surfaces that must enforce them. Rows are voice rules, claims, visuals, and disclaimers. Columns are channels and templates. You add locale exceptions, legal footers, and CTA patterns per surface. If a rule isn’t in the matrix, it likely won’t survive production.
This matrix becomes the single table everyone references. It tells design where disclaimers go on small screens. It tells product marketing which claims need citations on the pricing page. It tells social which character bands and verbs are allowed. Over time, this matrix is what prevents the "but I thought we could say that" thread from happening at all.
The hidden rules inside channel templates
Every channel hides constraints that quietly reshape your message: truncation thresholds, auto-inserted UTMs, default alt text, hard-coded CTAs, even line-height that breaks your rhythm. You can’t wish those away. Audit them. Then translate the findings into schema fields, tokens, and validations your CMS and email builder can enforce automatically.
When the template holds the rule, humans don’t have to remember it. More importantly, reviews stop catching formatting "gotchas" after copy is locked. You catch violations at compile time, not post publish.
Want to see what enforcement looks like in practice? If you’re already thinking, "we need this yesterday," Try Generating 3 Free Test Articles Now.
The Real Issue: Rules Are Not Mapped To Where Work Happens
The real problem isn’t your standards, it’s that they aren’t encoded in the places content gets created. Strategy decks explain why; they rarely specify which field stores the claim, which regex blocks a banned phrase, or which linter checks CTA verbs. Without that mapping, you’re relying on memory.

What traditional approaches miss about enforcement
Most governance lives in prose. "Use active voice." "Don’t promise outcomes." "Include a disclaimer for this feature in regulated markets." Helpful guidelines, sure. But prose doesn’t compile. Prose can’t block publish. What teams need is a map from policy to mechanism, field, token, linter, or build step, per channel.
This is where policy-as-code comes in. Prohibited terms become regex. Required disclaimers become schema fields. CTA patterns become a rule set in your component library. Put it in source control. Review changes like code. That way, "we updated voice last week" actually means "every template enforces it today."
Reference frameworks can help. The idea behind Standards and Governance guidance from SimpleA is the same: standards have to be operationalized, not admired.
Claims control depends on knowledge, not opinion
Approved claims shouldn’t be a vibe. They should be grounded in a knowledge base with provenance. Link each public claim to a KB source and version. Require citations for risky lines, numbers, and feature specifics. If a draft can’t resolve a citation, it fails the gate and returns for edit. Not a judgment call, just a rule.
This is where strategic governance shows its ROI. Teams that formalize claim provenance, voice rules, and enforcement patterns see fewer escalations and faster throughput, as outlined in Contentstack’s view on strategic content governance benefits. You’re not slowing things down. You’re preventing rework.
The Cost Of Drift Shows Up In Rework, Risk, And Reputation
Drift doesn’t send an invoice. It shows up as rework, delays, and avoidable meetings. Quantify it, and you’ll unlock budget for pre-publish checks. For example, if 20% of assets need edits after review, you’re paying for missing upstream guardrails. That’s not a people problem. It’s a system problem.
Let’s pretend we run the numbers for a quarter
Let’s pretend you ship 60 assets a month across web, email, and social. If 20% fail review and each one takes two hours to fix, that’s 24 hours of rework monthly. At a blended rate of $100 per hour, you burn $2,400 per month, $7,200 per quarter. And that excludes legal escalations, rollbacks, and opportunity cost.
Now imagine the tail risk. One risky claim leaves the building. Maybe it’s fine. Maybe it forces a retraction and a week of "what happened?" meetings. That risk is what pre-publish gates are meant to absorb. Not to slow you down, but to keep you from paying twice.
The downstream impact on trust and SEO
Inconsistency erodes trust. When a product page claims one thing and docs hedge another, buyers notice. So do crawlers and LLMs. Drift triggers duplicate content, schema mismatches, and crawl waste. Over time, your authority decays because your story isn’t stable or well-cited.
Multi-brand organizations feel this more acutely. The patterns of "content chaos" are well-documented, fragmented governance leads to duplication, off-voice pages, and untraceable claims, as outlined in multi-brand content governance challenges from dotCMS. The fix isn’t more content. It’s better constraints.
Still cleaning up after reviews? There’s a faster path. Shift checks upstream and let the system block the bad patterns. When you’re ready, Try An Autonomous Content Engine For Always-On Publishing.
Speed With Safety Requires Clear Owners And Runbooks
Speed and safety can live together when owners, SLAs, and a simple incident loop exist. The rule is straightforward: find, fix, codify. Freeze promotion when needed. Roll back or hotfix the claim. Convert the incident into a rule so that class of error can’t publish again.
When your launch thread contradicts the product page
We’ve lived this. A quick CEO post with a bolder claim than the product page. Slack lights up. Sales asks if it’s safe to use. Legal is worried about precedent. The fix isn’t heroics. It’s a pre-approved claims ladder and a rule that social must reference the same KB truth as web and docs.
On the governance side, make it multistakeholder by design. Marketing owns speed, product owns truth, legal owns risk. Give each a role, a time box, and a paper trail. That approach tracks with broader thinking on platform governance models, like the assessment framework for multistakeholder governance. You don’t need more meetings. You need lanes and clocks.
A Practical Way To Enforce Voice And Claims Across Channels
The pragmatic approach is simple: map, encode, validate, and operate. Build the matrix. Turn prose into tests. Add pre-publish checks. Close the loop with owners and SLAs. For example, require citation IDs for risky lines, enforce CTA verbs via tokens, and block publish when rules are violated.
Step 1: Build the governance to channel matrix
Start by listing every policy, allowed claim, disclaimer, and exception. Columns are your channels and templates: web CMS, docs, product pages, email, and social. For each cell, define fields, constraints, and what’s mandatory (e.g., citation IDs, locale-specific footers, CTA pattern). If it’s not in the matrix, it won’t be enforced.
Two notes from experience. First, resist the urge to overfit the matrix to a single campaign; design for the surfaces you own. Second, treat this as living documentation in source control so updates are reviewed and rolled out, not trapped in a deck.
Step 2: Translate voice and claims into channel tokens
Voice doesn’t need to be subjective. Compress it into tokens you can test: headline cadence, sentence-length bands, banned phrases, CTA verbs, even channel-specific rhythm rules for social. For claims, require citation IDs tied to KB sources. Store tokens and patterns in version control with owners and change history.
Once tokens are real, enforce them with linters per channel. A blog linter can flag passive constructions or off-voice openers. A docs build can fail when a feature claim lacks a citation. You’re not policing taste, you’re checking tokens resolve correctly, and citations exist and are in scope.
Step 3: Insert pre-publish checks into templates and schemas
Make checks unavoidable. Add metadata schemas and field validators to your CMS and docs pipelines. Hook linters into CI. Block publish when tokens are violated, prohibited terms appear, or citations are missing. The intent is simple: issues never reach a human reviewer if they fail the gate.
Do this right and "review" becomes a sampling function, not a firehose. It also aligns to high-level governance practices, codify standards so execution is consistent, as many standards bodies advocate. Your reward: fewer late-stage edits, less whiplash, and fewer "sorry to ping on a Friday" messages.
Step 4: Define gates, SLAs, and a remediation loop
Create role-based approval gates with SLAs per channel. Document an emergency override path with two humans and a clock. When a violation slips through, freeze promotion, fix it, and add a new rule so that pattern can’t publish again. Then measure: fewer incidents means your system is learning.
This is the operational backbone that lets a small team move quickly without rolling the dice. It’s management-light and repeatable. And because it’s encoded, new teammates don’t have to learn the hard way.
How Oleno Enforces Voice And Claims Across Every Channel
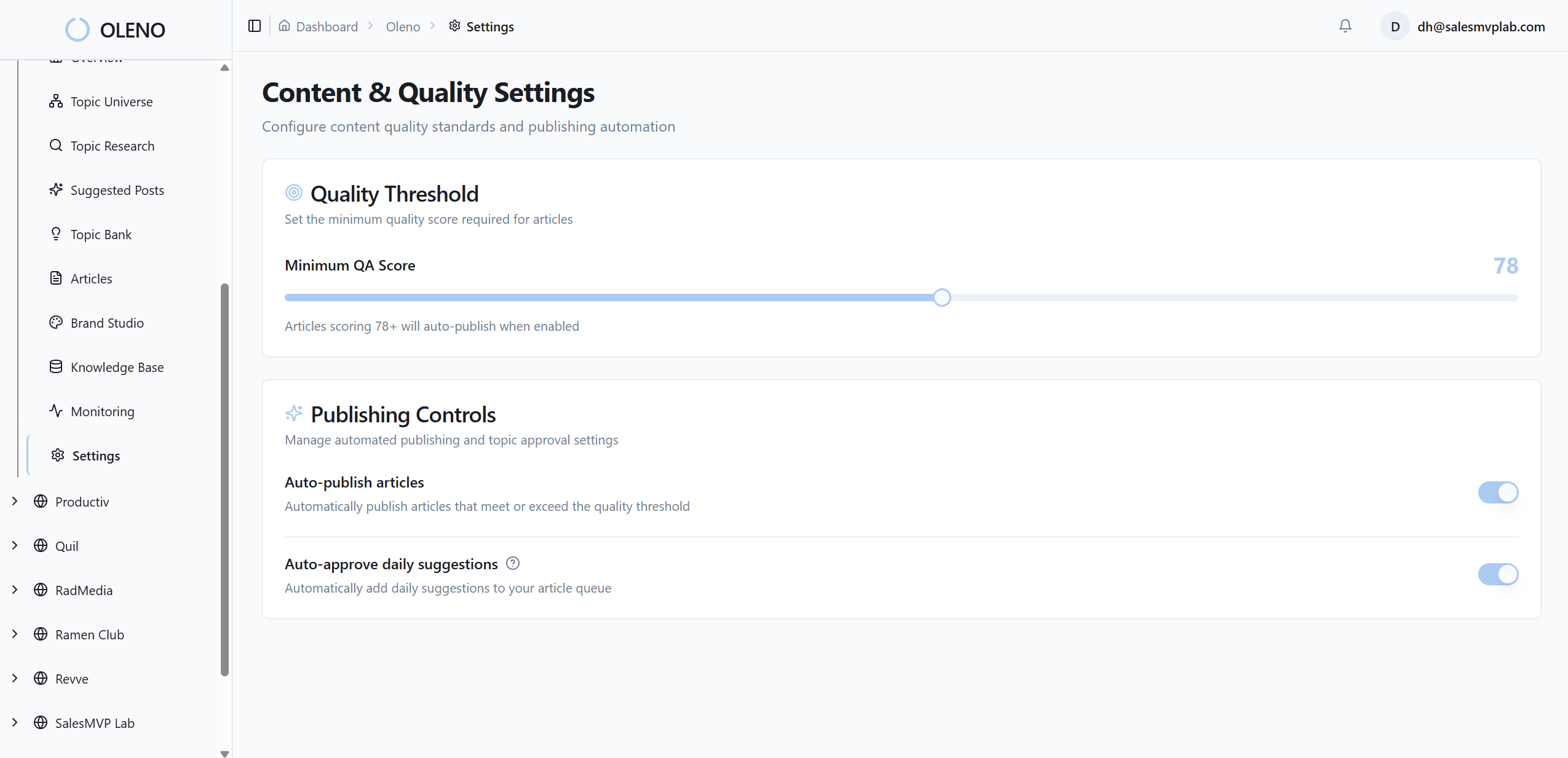
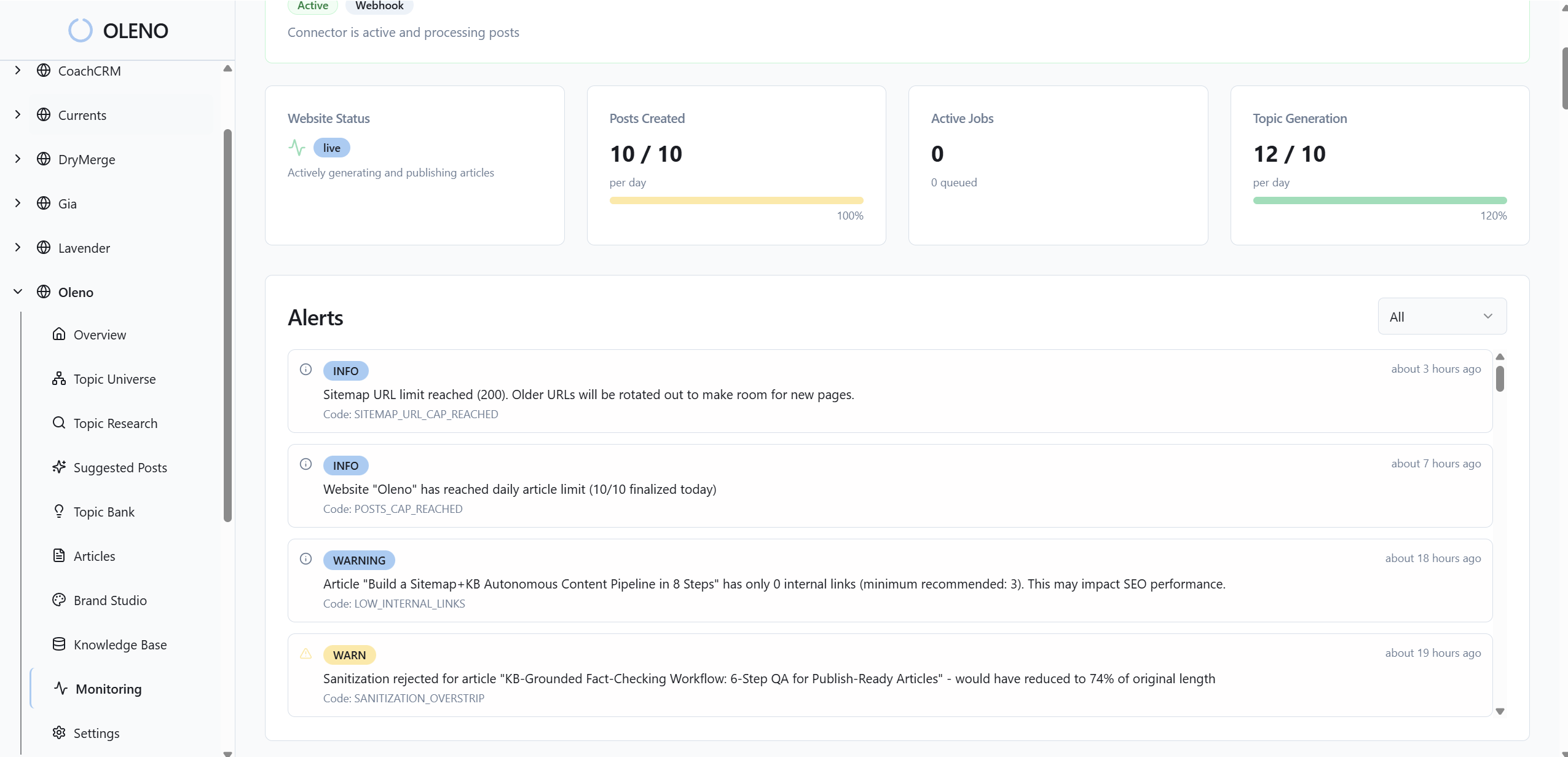
Enforcing voice and claims requires a system that encodes your rules and runs them at scale. Oleno was built for this: governance you configure once, deterministic pipelines, and pre-publish QA gates that apply across studios and channels. You set boundaries. The system enforces them before humans have to.
Governance to channel mapping you configure once
With Oleno, you encode voice, product truth, allowed claims, and CTA patterns up front. Those rules apply everywhere, briefs, drafts, visuals, and publishing, so outputs don’t drift as volume increases. Because governance is separate from creation, changes roll out consistently without requiring training cycles or team-wide reminders.
This follows a simple principle: define once, apply everywhere. As your channel mix evolves, the mapping evolves with it, not against it.
KB-backed claim validation with provenance-first retrieval
Oleno grounds risky lines in your knowledge base. Drafts reference approved claims and sources, and they fail the gate when a citation is missing or out of scope. This reduces invented features and keeps product pages aligned with docs and emails. When a source changes, you know exactly which assets need refresh.

The result isn’t promises. It’s fewer "where did that number come from?" threads, tighter alignment across surfaces, and cleaner handoffs to legal when something truly new needs review.
Pre-publish QA gates with role-based approvals and SLAs
Nothing ships without passing voice, narrative, accuracy, and structure checks. Oleno’s QA gates block publish when tokens violate your voice rules or claims lack citations. For channels that need a human in the loop, you can add role-based approvers with SLAs and an emergency override path. Speed and safety stop fighting each other in the last mile.
This replaces one-off reviews with a consistent bar. Reviews become the exception path, not the system itself.
Drift detection, sampling, and safe publishing
Oleno provides sampling to catch edge cases gates can miss, plus reliable CMS publishing with idempotency and retry patterns. If something slips, you can roll back, fix the source, and codify a new rule so that class of error can’t happen again. Over time, incidents decrease because the system learns what "good" looks like in your context.
That’s how you reduce rework hours and protect reputation without slowing down your calendar. Ready to put it to work on real assets? Try Oleno For Free.
Conclusion
Here’s the takeaway. Governance that lives in slides won’t survive channel translation. Move rules into templates, tokens, and gates. Map claims to citations. Give owners SLAs and a calm override path. Do that, and your reviews get lighter, your message gets steadier, and your team gets weekends back. You’ll still make judgment calls. You’ll just make them on purpose, not in a panic.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions