Policy-as-Code for Content: Automate Pre‑Publish Governance with Linters

Most teams treat governance like a PDF and a kickoff meeting. Then they wonder why voice drifts, claims get risky, and QA turns into a slog. Policy-as-code for content fixes that by turning rules into checks your system can run, every time. Think: your brand rules, written as tests a linter can run in your pipeline. You stop debating taste and start enforcing the playbook.
I learned this the hard way. When you scale output, drift sneaks in. One phrase tweak here, a stray claim there, a missing alt tag you didn’t catch. None of it looks fatal in the moment. Add volume and it compounds into rework, risk, and lost trust. Code catches what humans miss, and it does it without getting tired.
Key Takeaways:
- Convert human-facing rules into a prioritized, testable policy catalog that your pipeline can enforce.
- Wire a simple, runnable architecture: CMS webhook to CI job to linter to publish gate.
- Start with high-impact linter checks: forbidden claims, tone triggers, required metadata, and alt text.
- Choose smart fallbacks: auto-fix where safe, route to human review where judgment matters.
- Version policies, assign owners, and audit violations monthly so standards don’t decay.
- Track success: baseline fail rate, time-to-publish, percent auto-fixed, and review churn.
- Expect fewer pre-publish failures and faster reviews once the guardrails run by default.
Why Policy-as-Code for Content Beats PDFs
Policy-as-code for content wins because code enforces rules, while PDFs ask people to remember them. Systems can test voice constraints, claim boundaries, and metadata on every draft. Humans forget, especially at speed. Teams that encode rules stop drift before it ships. A linter (an automated checker) runs the same way, every time—no fatigue, no guessing.
Governance Drift Starts Small, Then Gets Expensive
Voice drift rarely starts with a glaring mistake. It starts with a synonym that feels off, a CTA that doesn’t sound like you, a claim that edges past what legal approved. One or two slip through. Multiply by 40 assets in a month, and you’ve got a pattern you didn’t intend. I’ve watched teams spend more time cleaning up near-publish than creating net-new work. That is a tax. And it is avoidable.
Policy-as-code turns that soft guidance into hard checks. If a term is banned, the linter blocks it. If a product claim isn’t on the allowlist (pre-approved statements), it fails the build. If alt text is missing, the job kicks it back. Nothing subjective, no arguments about “close enough,” just rules running at the edge of publish.
You still need taste. You still need editors. But they work on meaning and story, not hunting for missing UTM tags or cleaning up stray phrasing that your brand never uses.
Rules That Live in Docs Don’t Change Behavior
Docs tell you what good looks like. Code changes what actually ships. If your rules only live in Notion, they rely on memory, which is fragile. If your rules live in the pipeline, they create habits. People learn faster when the system gives instant feedback at the point of failure.
I like fast feedback loops because they remove mystery. The draft fails, you see why, you fix it, you move on. After a few cycles, writers stop making the same mistake. That is how quality compounds without adding meetings or headcount.
The Real Problem: Rules You Can’t Enforce
The real problem isn’t that your team forgets. It’s that your rules aren’t executable. If you can’t test a standard, you can’t enforce it. That gap between “should” and “will” is where drift, risk, and wasted review hours live.
Symptom vs. Cause in Content Ops
The symptom is slow reviews and off-brand drafts. The cause is non-testable governance. When standards exist only as prose, editors must translate guidelines into judgment calls every time. That is slow, error-prone, and impossible to scale. You think the fix is “more eyes.” It isn’t. It’s fewer manual checks and more machine checks.
Translate rules into conditions. “Never say X” becomes a denylist (blocked terms). “Always include alt text and metadata” becomes a required-field test. “Only claim Y in these contexts” becomes an allowlist tied to product truth. Once you can write it as a rule, you can run it.
Where Manual Checks Collapse
Manual checks collapse under three loads: volume, speed, and variance. Volume creates fatigue. Speed compresses review windows. Variance introduces edge cases that humans miss when rushing. I’ve seen final-hour reviews let risky phrasing slide because the team needed a ship. You can’t build reliable demand gen on exceptions. You need a gate that’s boringly consistent.
This is why dev teams embraced policy as code years ago. Tools like Open Policy Agent didn’t win because they were trendy. They won because rules as code scale without getting sloppy.
The Cost of Manual Governance in Content Ops
Manual governance carries a clear cost: time, risk, and opportunity. You can measure each one. When you do, the case for automation writes itself.
The Time Tax You Can Measure
Every manual review adds minutes. Each “quick fix” adds handoffs. I’ve seen teams burn 20 to 40 minutes per piece on basic checks alone, which adds up fast across a weekly cadence. That time rarely improves the story. It just patches preventable misses. Even if you’re conservative, a few hours a week go to chores machines can do instantly.
Baseline the before/after so you can prove lift:
- Average pre-publish failures per 10 assets
- Average minutes per asset on basic checks
- Percent of pieces blocked for claims or accessibility
- Cycle time from draft saved to publish-ready
Tie that to pay rates and monthly output and you get a hard dollar number. Then compare that to a one-time setup of policies. The breakeven happens faster than you think, especially when evaluating policy-as-code for content.
The Risk That Hides in Plain Sight
Risk hides in three places: unapproved claims, missing context, and accessibility gaps. An off-limits feature mention can trigger trust issues or legal headaches. Vague wording without sources chips credibility. Missing alt text or captions blocks audiences and invites compliance risk. A linter never gets tired of checking the same thing. Humans do.
If you need a simple starter rule set, use what the web already expects. For example, the W3C’s alt text decision tree gives a clear standard you can turn into a check. No debate, just a requirement that passes or fails.
The Opportunity Cost on Pipeline
Slow reviews delay publishing. Delayed publishing slows testing loops. Slow loops delay learning. That is lost pipeline. The hidden cost isn’t just hours spent fixing commas. It’s the month you miss a cluster because everything stuck in approvals. Policy-as-code for content accelerates cycle time, which compounds learning and output.
What It Feels Like When Governance Fails for Policy-as-code for content
It feels chaotic. It feels like you’re always behind. You start to question whether the team can keep up, even though everyone’s working hard. That’s the part that stings.
The Friday Night Rewrite
You know the one. Big post goes live Monday. Late Friday, someone spots an off-limits claim and a few lines that don’t sound like you. Now it’s a scramble. Slack pings, shared docs, version hell. The fix bleeds into the weekend. Nobody’s happy. The trust hit is worse than the time hit.
A gate would have blocked the claim the moment it appeared. A tone check would have flagged the phrasing before humans even saw it. The rewrite becomes a two-minute correction midweek, not a fire drill at 9 pm.
The Approval Chain That Never Ends
Another classic. Draft, review, edit, review again, escalate, add comments, repeat. People aren’t wrong, they’re protecting the brand. But you’re paying the price in time and morale. When clear, enforced rules handle the basics, approvers can focus on real judgment calls and move faster. Less back-and-forth. Fewer “can we wordsmith this again?” loops.
The New Way: Policy-as-Code for Content, From Draft to Publish
The new way turns guidelines into a runnable system. You define rules once, wire them into the pipeline, and let the gate do its job. Content still needs human taste, but the system carries the boring parts.

Build a Policy Catalog You Can Test
Start with a simple catalog of rules written as conditions, not wishes. Rank by impact and ease of detection. If a rule is ambiguous, tighten it until a machine can decide.
The first batch should be concrete:
- Forbidden terms and risky phrases, mapped to safer alternatives
- Allowlisted product claims, tied to a source of truth
- Required metadata fields, like title length, description, canonical, and OG tags
- Accessibility basics, like non-empty alt text and descriptive filenames
- Voice and CTA style constraints, with examples to check against
As you see violations, refine the rules. If a policy causes noisy false positives, fix the policy, not the people.
30-day quick start (keeps momentum high):
- Week 1: Inventory current standards; pick top 10 rules by risk/impact; assign owners.
- Week 2: Encode rules; decide auto-fix vs human review; set pass/fail thresholds.
- Week 3: Pilot on one content stream; capture fail rate, minutes saved, and common violations.
- Week 4: Tune rules to cut noise; roll out to the next stream; add monthly audit.
Architecture: CMS to Linter to Gate
Keep the architecture boring. Boring ships. Content saved in your CMS or repo triggers a webhook. That fires a CI job. The job runs your linter, posts results, and either blocks or passes to publish.
A simple path looks like this:
- Save or update draft in CMS or repo.
- Webhook triggers a CI job in your provider.
- Linter runs policy checks and collects violations.
- Auto-fix safe items, like metadata or minor phrasing, especially when evaluating policy-as-code for content.
- Fail the job for risky items, post a clear report, and stop the publish.
- If all checks pass, publish or stage as draft automatically.
If you need a place to wire the webhook-to-job step, the GitHub Actions documentation shows exactly how to run checks on content events. Nothing fancy required.
Fallbacks: Auto-Fix vs Human Review
Not every violation deserves a block. Some deserve a silent fix. Others require human eyes. Your fallback strategy decides what flows and what stops.
Use a simple split:
- Auto-fix when the correction is deterministic and low risk, like swapping a banned term or adding a missing tag.
- Human review when the change affects meaning, positioning, or legal exposure, like a product claim or competitor comparison.
Role clarity helps:
- Policy owners update rules and thresholds monthly.
- Editors review meaning-level exceptions.
- Ops monitors false positives and pipeline health.
If you’re unsure, favor human review at first. Over time, you’ll earn the right to automate more.
Ready to see this wired end-to-end without building it yourself? Request a Demo.
Solution: How Oleno Makes Policy-as-Code for Content Real
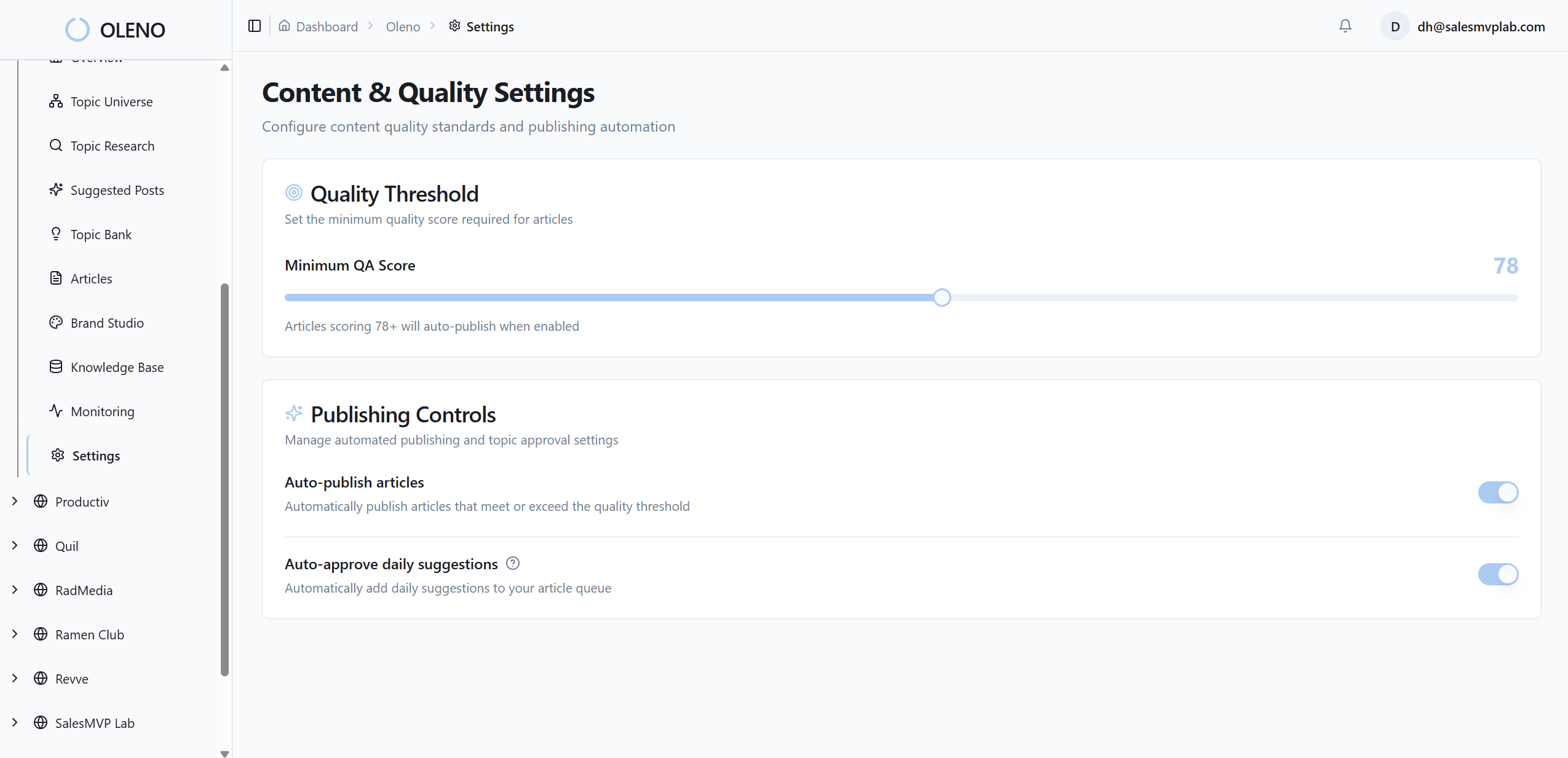
Oleno operationalizes policy-as-code for content by encoding your voice, narrative, and product truth, then enforcing those rules before anything publishes. You still own the standards. Oleno turns them into a system that runs on schedule, catches drift, and blocks risky claims before they escape review.

Governance That Becomes Executable
Brand Studio captures tone, terminology, CTA style, and structural constraints as machine-readable rules. Marketing Studio encodes what you want the market to understand, so every asset reinforces your point of view. Product Studio locks in allowed claims and feature boundaries, so content stays accurate and safe. Knowledge Archive Grounding provides the approved references that QA uses to check facts.

What used to take a day of reviews collapses into a predictable gate. If a draft violates the rules, Oleno flags the exact lines, then either auto-corrects simple misses or routes the piece back with a clear report.
- Brand Studio: voice, term lists, CTA patterns, and structure checks become enforceable rules.
- Marketing Studio: message pillars and narrative frames prevent off-message drift.
- Product Studio: allowlists and denylists stop invented features or shaky claims.
- QA Gate Before Publishing: rule-based and model checks block low-quality or ungrounded output.
Teams aiming to cut manual QA hours in half can use Oleno’s gate to move routine checks out of meetings and into code. Want numbers you can show your exec team? Request a Demo.
Pipelines That Ship Without Babysitting
Oleno runs deterministic pipelines from brief to draft to QA to publish. The rules you defined in governance run automatically during Brief and Draft. The QA gate blocks anything that fails voice, structure, grounding, or readability. CMS Publishing pushes approved content as drafts or live posts, no copy-paste, no last-mile errors.
If you’ve watched content pile up waiting for approvals, this is the relief valve. The system carries the checks, so humans focus on story and strategy again.
Practical Callback to the Costs
Remember the time tax and risk we talked about earlier? Oleno targets those directly. Auto-fixes remove the easy misses that used to burn 20 to 40 minutes per piece. The allowlist and denylist checks reduce risky claim exposure. The accessibility rules keep basics like alt text from slipping. Cycle time drops because drafts either pass cleanly or come back with precise fixes, not vague edits.

If you want to see your policies turned into a running gate, not just good intentions, Book a Demo.
Conclusion
Governance that lives in docs will always lose to deadlines. Encode the rules, wire a linter, and let the gate do the boring work. Start with a small policy catalog, connect CMS to CI, and choose clear fallbacks. Track fail rate, minutes saved, and cycle time so you can prove the lift. Most teams can reduce pre-publish failures by a wide margin once policy-as-code for content is in place. The upside is simple, faster cycles and fewer late-night rewrites. The work gets calmer. The output gets stronger. And your story stays yours.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions