Policy-as-Code for Marketing Governance: Automate Claim Checks & Rollbacks

You can write faster. That’s not the bottleneck. The bottleneck is enforcing what’s true about your brand and product every single time, without late edits or “did anyone check with legal?” moments. Policy-as-code is how you stop debating rules in meetings and start enforcing them in the places that matter: PRs, staging, and pre-publish.
I learned this the hard way on small teams. We moved quickly, shipped a lot, then one line forced a rollback and a pile of rework. Not a crisis. Just avoidable churn. The fix wasn’t a better editor or another prompt. It was turning recurring edits into rules encoded in versioned files, with gates that run every time.
Key Takeaways:
- Treat brand and claim rules as code that blocks merges and publishes
- Model claims with owners, evidence, and expiry so truth is queryable
- Track failure patterns to tune policy, not just coach authors
- Automate rollbacks with idempotent actions to prevent distribution chaos
- Start small: schema + registry + CI checks + staged releases
- Use deterministic QA gates to keep cadence stable as volume grows
Manual Reviews Do Not Scale And They Quietly Drift
Manual reviews break under load because each person interprets rules differently and checklists slip during crunch time. Policy-as-code converts guidelines into deterministic checks that run on every PR and pre-publish. Think banned superlatives blocked at merge, not debated in Slack. The difference is reliability, not more rules.

What Is Policy-As-Code For Marketing, Really?
Policy-as-code for marketing means you encode brand voice constraints, claim boundaries, required CTAs, and structure into machine-readable rules. You store those rules in a versioned repo, run them in CI, and block merges or publishes when they fail. It’s the same concept DevOps teams use to keep infra safe—just pointed at your content.
The important nuance: you’re not trying to write with code. You’re defining guardrails once so the system checks them consistently. Style guidance becomes lint rules. Claims become resolvable IDs. Structure becomes schema validation. If a guideline matters, encode it. If it’s optional, make it a warning. Deterministic beats interpretive at scale.
If you want a mental model, think of how infrastructure teams converted manual approvals into policy engines. The pattern translates. Start simple and make it legible. Frameworks in the DevOps world like Red Hat’s overview of policy-as-code automation show how shifting checks left reduces last-minute firefighting.
Why Human Gates Break At Volume
Human gates scale linearly. Volume does not. When you try to keep up with checklists and reviewer availability, you get drift. Two reviewers read the same rule and enforce it differently. Deadlines compress. Someone waves a piece through to keep the calendar intact. Then legal sends a note on publish day. You’ve been there.
The root problem is interpretive enforcement. People try to remember rules under pressure. Even great editors miss things when they’re juggling twelve tabs and a launch deck. Your goal is not to replace judgment. It’s to reserve judgment for narrative decisions—positioning, argument, angle—while machines enforce the non-negotiables every time.
When checks move left into CI and staging, a lot changes. Authors get instant feedback. Editors stop playing traffic cop. And you create an auditable trail of what failed, why, and how it was fixed. That’s how you reduce rework without slowing anyone down.
Where Teams Misread The Problem
Most teams try to speed up drafts. Faster prompts. Better templates. Fewer rounds. That helps a little, then quality drifts. The problem isn’t drafting. It’s that your governance lives in docs and slides instead of rules that run automatically where publishing decisions happen.
Once you encode rules, you shift the conversation. You don’t argue about a banned term after the fact. You fail the build before it reaches staging. You don’t debate whether a claim is supported. You look it up in the registry and either reference the approved phrasing or create a PR to add it. That’s how you stop repeating the same fix.
Ready to skip the theory and feel the speed of automated checks? Try a small experiment, then expand. Want to see what a governed flow looks like in practice? Try Generating 3 Free Test Articles Now. Try Generating 3 Free Test Articles Now.
The Hard Part Is Claims, Not Tone Or Formatting
Tone is subjective; claims aren’t. If something could be challenged—market share, performance, comparisons—encode it. Treat claims as entries with owners, evidence, and expiry dates. Your linter should detect claim usage and validate phrasing against the registry before anything ships. That’s how you keep truth consistent without meetings.

What Claims Need Machine-Readable Truth?
Anything that asserts performance, comparisons, counts, or time-bound statements needs a structured record. “Fast,” “best,” “only,” and “market-leading” are obvious red flags. But the subtle ones matter more: “reduces review time by 30%,” “used by 1,200 teams,” or “publish in two clicks.” Those are checkable. So make them checkable.
In practice, you store claims as objects: ID, approved phrasing, owner, evidence link, review cadence, and status. Authors reference by ID when they draft. Linters verify that the phrasing in the draft matches the approved form and isn’t expired. If the phrasing drifts, the build fails. It’s boring. It’s effective.
This mirrors how policy engines validate infra changes against a set of rules. The idea isn’t new. The marketing use case is just under-served. If you want to sanity-check the approach, look at governance models like HashiCorp’s Sentinel policy-as-code framework for a reference on policy design patterns.
How Do You Model Provenance And Ownership?
Ownership reduces debate. Each claim needs a named owner (usually product marketing or legal), a source of truth, and a review cadence. Store evidence links—docs, screenshots, customer approvals—and an expiration date. When phrasing changes, capture who approved it and why. That turns “who said this?” into a lookup, not a DM.
The other piece is lifecycle. Claims should have statuses: proposed, approved, sunset. Your workflow should make it easy to propose a new claim, route it to the right owner, and update the registry with approved language. When a claim sunsets, drafts that reference it should fail with a helpful message. A little friction early saves days later.
One more nuance: make the registry easy to read for non-engineers. YAML or JSON with comments works fine. If legal can review a PR and understand it in five minutes, the policy will keep getting better instead of turning into a gate nobody wants to touch.
Why A Registry Beats Scattered Docs
Docs drift. Wikis get stale. Spreadsheets fork. When truth lives in scattered places, authors guess or copy old phrasing. That’s how “we support X” turns into “we guarantee X” over a quarter. A registry that feeds your linter creates a single place to update reality. Change it once; the system enforces it everywhere.
You’ll still need judgment in the narrative. That’s good. But you don’t want to re-litigate the same facts. A registry turns facts into a service. Authors pull from it. CI validates against it. And when legal asks “where did that number come from?” you open the entry and show the approver, the evidence, and the last verification date. No hunting.
One small tip: version the registry and surface diffs during review. Visibility builds trust. When people can see exactly what changed and why, they’ll participate instead of bypassing the system.
Drift, Rework, And Risk Add Up Faster Than You Think
Rework scales faster than you think. Let’s pretend 20% of posts need late claim edits and each cycle burns 45–90 minutes across writer, editor, and approver. At 20 posts a month, that’s roughly 9–18 hours gone, plus missed slots. Encode checks early and those edits never make it to staging.
What Does Rework Actually Cost When Volume Increases?
Let’s pretend you publish 20 assets a month. Six need claim changes post-approval. Each fix requires: author rewrite (20 minutes), editor re-review (15 minutes), approver signoff (10 minutes), republish coordination (10 minutes), and distribution cleanup (10 minutes). Call it 65 minutes per incident. That’s roughly 6.5 hours a month in pure churn.
Now add the hidden costs. Calendar shuffles. Social updates. Sales asking “is this link still safe to share?” Multiply by quarters and your cadence erodes. You didn’t write fewer pieces because you ran out of ideas. You wrote fewer because you had to redo the same ones. Machines are very good at preventing this specific pattern.
When checks fail earlier—on commit, on PR, on staging—authors fix in flow. The asset never hits your CMS in a questionable state. Cadence stabilizes, and teams stop budgeting “rollback time” into the week.
How Do Missed Checks Show Up In Metrics?
If you’re not measuring policy performance, you’re guessing. Track failure rates by rule category (claims, structure, banned terms), average remediation time, and first-pass publish rate. If banned phrases slip through staging, your checks aren’t early enough. If claim failures spike after a product update, your registry and review cadence are out of sync.
You can also watch rework-to-publish ratios and how often rollbacks occur per quarter. Patterns matter more than one-off incidents. This is similar to how DevOps teams evaluate policies in CI/CD. For a practical starting point on thinking about policy metrics, see the principles outlined in AWS’s practical guide to policy-as-code.
One interjection. Don’t turn metrics into punishment. Use them to tune the system, not blame authors. If a rule is firing too often, improve the rule or the registry entry it’s tied to.
Why Manual Rollbacks Create Secondary Damage
Rollback isn’t just switching a post to draft. It touches distribution queues, email content, social previews, and sales collateral. People stop trusting links. Context gets lost in the scramble. And someone inevitably leaves an old asset live in a corner of the site. That’s how small mistakes get loud.
Automate the rollback path. Define clear criteria for what triggers it, ensure CMS actions are idempotent (no duplicates, clean state), and update distribution queues in the same flow. Record the event in an audit log so you can fix the rule or registry entry later. When rollback is a script, not a meeting, your calendar keeps moving.
Still firefighting rollbacks by hand? You don’t have to. If your checks run early and your publishing actions are reliable, these incidents become rare and short-lived. Want help automating the boring parts so your team can focus on story, not surgery? Try Using an Autonomous Content Engine for Always-On Publishing. Try Using an Autonomous Content Engine for Always-On Publishing.
The Moment Everything Stops Because Of One Line
One banned phrase can stall a week. You ship, legal flags a risky superlative, and the calendar freezes. Sales asks for a fix. Leadership wonders what else slipped. If that phrase lived in a banned list enforced by CI and pre-publish checks, it never would’ve reached your CMS. Simple, but it matters.
When A Banned Phrase Slips Through, What Happens?
You publish at 10am. By noon, you get the note: “We can’t say ‘only’ here.” Now you’re yanking links, pausing paid, and DM’ing sales. Nobody’s happy. Not because the line was malicious, but because the system didn’t catch it where it should: on commit, on PR, and again on staging.
The fix is deterministic checks. Maintain a banned-terms list with severity levels. Fail hard on non-negotiables. Soft-warn on preferences. Give authors remediation tips. If a phrase triggers on staging, block pre-publish actions automatically. You’ll still make mistakes occasionally. They won’t cascade across channels.
Policy engines in security use the same pattern. Marketing just needs to adopt it. For a plain-English overview of policy-as-code concepts, this SentinelOne primer is a helpful orientation.
A Small-Team Story You Might Recognize
We were three people covering launches and content. Move fast or miss the window. One week we shipped a piece with a claim that didn’t match the latest product reality. Not a big miss—just enough to trigger rework. Publishing paused, distribution paused, sales paused. Frustrating rework, right when we had momentum.
We turned the fix into a rule. The specific phrasing went into the claim registry with an owner and an expiry date. The linter started checking for it. The next time, the build failed before anyone had to jump on Slack. Fewer late edits. Fewer worried DMs. A little structure changed the week.
That’s the pattern. Turn recurring edits into rules. Let machines catch the repeatable stuff so humans can focus on the narrative.
Who Owns The Fix When Reviewers Are Overloaded?
Ownership should live in policy. Each rule needs a maintainer and an escalation path. When reviewers are slammed, the system still runs. If a rule misfires or becomes too noisy, the owner tunes it in code, updates the claim registry, and the next CI run enforces the new truth. No meetings required.
This also avoids the “who approved this?” spiral. If every rule and claim has an owner, you know exactly who to pull in and how to route the change. Over time, your review load drops because you’re improving the system, not inspecting every asset manually.
That’s how small teams stay sane. They push judgment where it adds value and codify the rest.
A Production-Ready Pattern You Can Ship This Quarter
Ship a minimal policy system in four pieces: a schema for rules, a claim registry with owners, CI checks wired to block merges, and staged publishing with safe rollbacks. Start small, keep rules readable, and evolve as you learn. The point isn’t perfection. It’s reliable enforcement that improves weekly.
Design The Policy Schema For Marketing Content
Start with JSON or YAML that defines rule types: banned terms, required CTAs by page type, allowed claims with IDs, structural checks for headings and snippet-ready intros. Include fields for severity, remediation hints, and owners. Make it human-legible—marketing and legal should be able to read and review it easily.
Version control is your friend. Every change should be diffed and reviewed just like code. Tie schema updates to real incidents: if a phrase caused rework twice, it gets a rule. Keep your first pass small; you can expand once the pipeline is working and people trust the process.
As the schema stabilizes, consider these common fields:
- rule_id, type, severity, owner, escalation
- description, remediation_hint, examples
- match_pattern, scope (draft, staging, publish)
- enabled, created_at, updated_at
Build The Claim Registry And Approval Flow
Give each claim an entry with owner, evidence links, approved phrasing, status, and sunset date. Make it easy to propose, review, and approve new entries via PRs. When product or legal updates a claim, authors shouldn’t have to guess. They pull the latest phrasing by ID, and your linter verifies it’s still valid.
Keep the approval commits clean. Who approved. When. Why phrasing changed. That’s your audit trail. When a claim sunsets, fail any draft that still references it with a clear message and a link to the replacement. You’ll remove ambiguity without slowing anyone down.
One more tip: show claim usage stats. If one claim causes frequent failures, it probably needs clearer phrasing or a broader example set. Policy isn’t static; it gets better with data.
Integrate Static Checks Into CI And CMS Staging
Wire your linter to run on PRs for fast feedback. Fail hard on claims and restricted language; soft-warn on voice and style. On merge, validate structure and claims again. In CMS staging, run a policy job that checks rendered HTML for template drift, schema markup, and CTAs before publish.
Keep logs per rule with pass/fail counts and remediation time. Over a month, you’ll see where the noise is and where the guardrails are saving you hours. For implementation patterns and governance concepts, the Harness governance overview maps neatly to what you need in content pipelines.
Make the feedback loop short. If authors can fix in the same session they draft, you’ll maintain pace and improve quality at the same time.
Implement Canary Publishing And Safe Rollbacks
Gate production behind staged releases. Publish to a safe section or a small audience first. Monitor rule compliance on the rendered page, not just the markdown. If a violation appears post-render, trigger an automated rollback that’s idempotent, updates distribution queues, and records the event for later tuning.
Feature flags help in complex setups, but you don’t need to over-engineer this. Start with draft vs live control and a clean rollback script that removes or reverts assets without duplicating anything. If you’re exploring tools, a quick survey like Spacelift’s overview of policy-as-code tools gives you a lay of the land that’s adaptable to content workflows.
The goal is simple: fewer surprises, faster recovery, and a cadence that doesn’t stall when one line goes sideways.
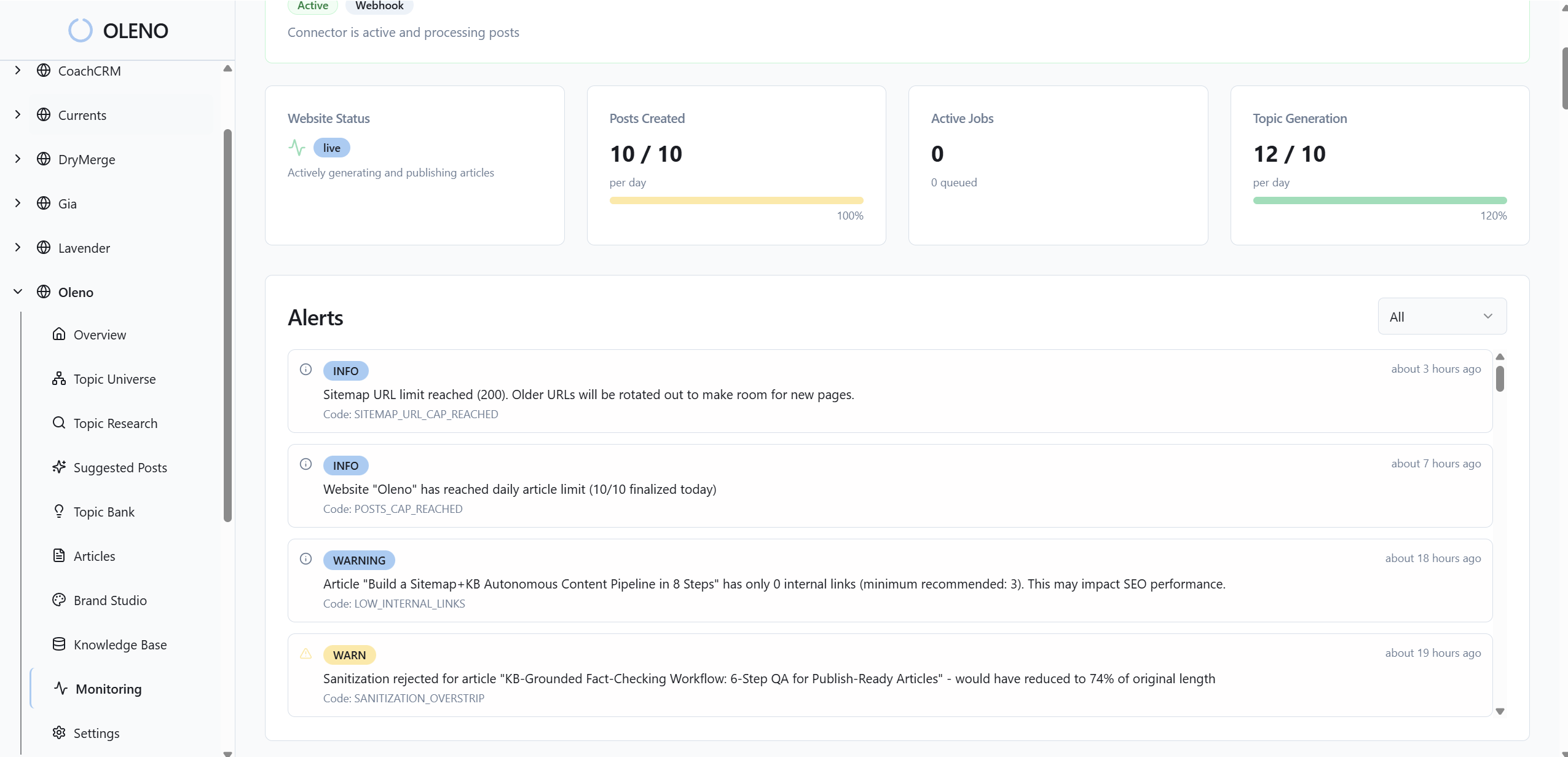
How Oleno Enforces Governance From Draft To Publish
Oleno lets you define narrative, voice, product truth, and safety rules once, then applies them across jobs—drafts, briefs, and final pages inherit the same constraints. A pre-publish QA gate blocks anything that doesn’t meet the bar, and CMS publishing is idempotent so rollbacks are clean. That’s how cadence stays steady.
Governance Encoded As Rules That Apply Everywhere
With Oleno, governance starts the system, not the draft. You define brand voice, approved claims, and narrative rules once. Oleno applies them automatically across the demand-gen jobs you enable—acquisition, education, evaluation, product marketing. That consistency prevents drift when priorities shift or new contributors join.
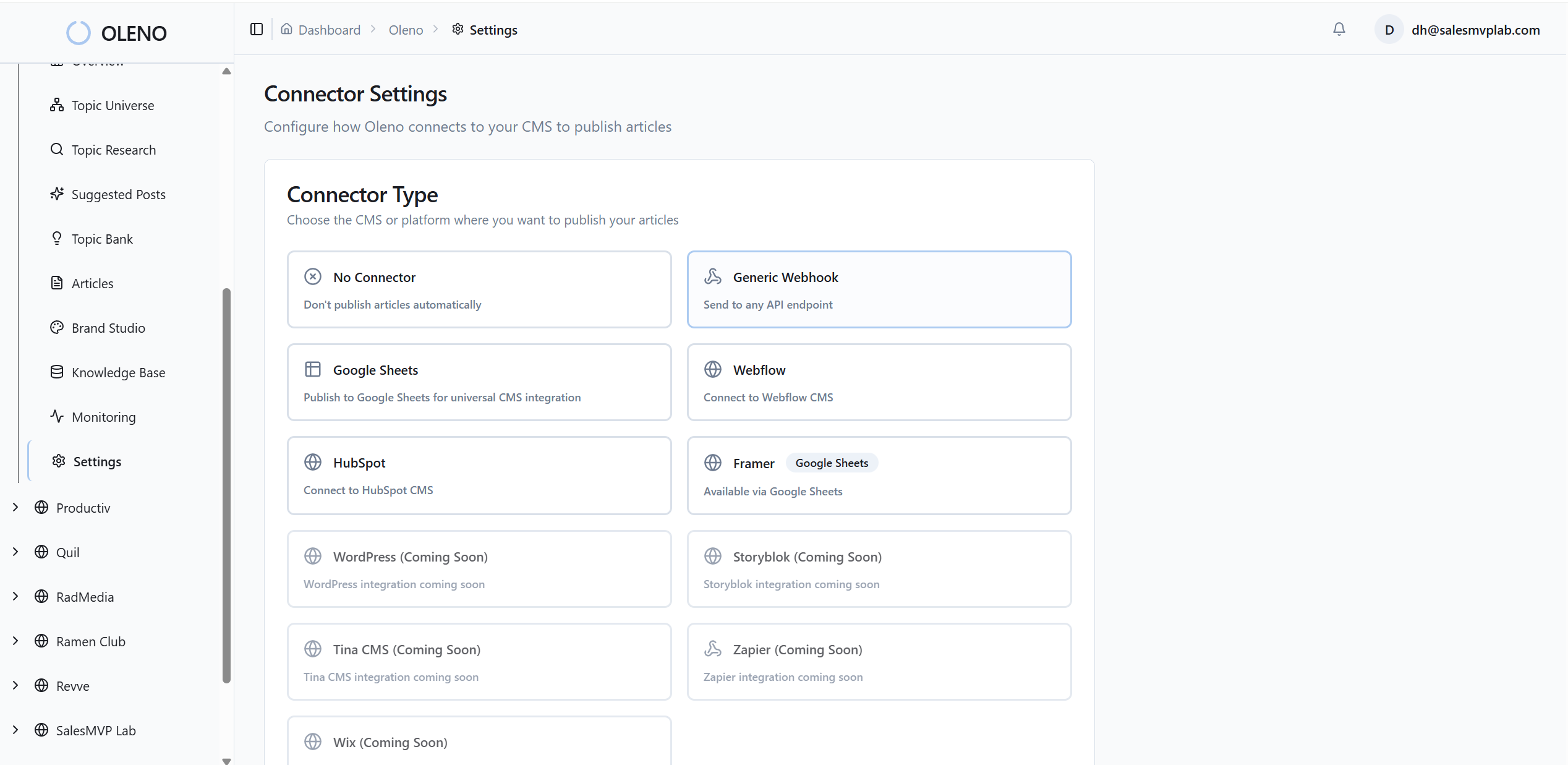
Because rules live in the platform, you aren’t relying on memory. Authors get consistent constraints no matter which asset they’re working on. Strategy stays human. Execution becomes reliable.
QA Gates That Block Until Content Meets The Bar
Nothing publishes in Oleno without passing a QA gate. The gate checks voice and tone alignment, narrative structure, clarity, grounding to your knowledge base, and safety constraints like claims and restricted language. If a draft fails, it’s revised automatically until it passes or flagged to the owner with specific feedback.

This removes the late-edit scramble you felt in the rework math earlier. Fewer last-minute changes. More first-pass publishes. And reviews focus on story and accuracy, not comma policing.
Idempotent CMS Publishing And Staged Releases
Oleno publishes directly to your CMS—WordPress, Webflow, Storyblok, HubSpot, and more—with idempotent actions to prevent duplicates. You choose draft or live. You can stage updates safely, then expand. If something needs to roll back, Oleno reverts cleanly without leaving orphaned assets or broken links, so distribution and sales can keep moving.
The point isn’t just speed. It’s reliability. Your pipeline should be boring and predictable so the narrative can be bold.
Operational Visibility To Tune Rules Over Time
Oleno gives you visibility into output volume, quality trends, and common failure patterns. You’ll see where rules fire, how remediation time changes, and where governance needs to tighten or loosen. That’s how the system compounds—fewer surprises, stronger narrative, and a cadence that holds even when people get pulled into launches.
If you’ve been wrestling with manual checks and late rollbacks, this is a different way to run. Let Oleno handle the repeatable enforcement while your team focuses on the arguments only humans can make. Ready to try it without a heavy lift? Try Oleno for Free. Try Oleno for Free.
Conclusion
Here’s the bottom line. You don’t need more prompts. You need rules that machines enforce and people can trust. Encode claims and structure. Run checks early. Roll back safely when needed. Then keep tuning. Whether you use Oleno or roll your own, policy-as-code turns “we hope it’s right” into “we know it ships right.” That’s how small teams win.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions