Secure AI Integrations: Protect Customer Data in Content Ops

Most teams wire AI into content ops like it’s just another plugin. That’s how leaks happen. Not because the model is “bad,” but because your inputs, retrieval scopes, and logs don’t have guardrails that fire every single time. You don’t need drama. You need a system.
I’ve been on both sides of this. At LevelJump, small team, three hats each. We recorded the CEO, transcribed, shipped. Fast. But brittle. At PostBeyond, I wrote fast because I had a framework. When the team grew, quality dipped, because context and structure lived in my head. Fragmentation kills consistency. AI just exposes it faster.
Key Takeaways:
- Treat AI connectors like part of your data system, not a plugin
- Redact at the edge, scope retrieval narrowly, require citations first
- Encode vendor policies in contracts and config, then audit, don’t trust
- Quantify the cost of leaks: rework, legal loops, and engineering tax
- Build a secure-by-default workflow: redaction logs, prompt snapshots, approvals
- Use deterministic pipelines and QA gates to reduce mistakes and anxiety
Ready to see a safer pipeline in practice? Try a low-risk run and validate your guardrails end-to-end. Try generating 3 free test articles now.
Why AI Connectors Create Data Risk In Content Ops
AI connectors create data risk because they’re treated like simple add-ons, not data paths. Sensitive fields slip into prompts, retrieval pulls the wrong fragments, and logs store more than you expect. The fix starts with boundaries: inventory inputs and outputs, define rules at the edges, and verify they run on every execution.

The Pitfall Of Treating AI Like A Plugin
When teams drop an LLM into the stack like it’s an SEO plugin, blind spots multiply. Prompts carry emails. Retrieval scopes reach into shared docs. Logs keep raw payloads longer than anyone realized. None of this is malicious. It’s what happens when connectors are added without a system view.
The right mental model is pipelines, not features. Where can sensitive data enter? Where might it exit? What are the side channels? Put policy at the boundaries, not in a wiki. Then enforce it in code. In my early runs, we shipped content fast, but review and structure lived in people’s heads. That worked—until it didn’t.
Treat every connector as a data surface. Redact at ingress. Mask at rest. Prove controls fired with artifacts you can show during a review. Activity isn’t safety. Systems are.
What Teams Overlook About Prompt-Safe Retrieval
Retrieval scopes decide what the model can “see.” Broad scopes invite trouble. You don’t want CRM notes and sensitive fragments pulled into a draft because a query was too generous. Narrow scopes reduce both hallucinations and accidental exposure. It’s pragmatic security. It’s also better quality.
Design for claim control. Filter at the claim level, not just the document. Reject statements without a valid source. Return citations first, answer second. This flips the workflow. The model assembles evidence before it writes. That approach echoes guidance like Secure AI principles from Salesforce, which stress guardrails, not blind trust.
Tie every chunk to provenance. Use IDs that trace back to a specific, approved source. Reviewers should be able to click back to evidence in seconds. That alone saves hours of back-and-forth.
What Is The Fastest Way To Stop Leaks Today?
Start at the input. A rule-based scrubber strips emails, phone numbers, IDs, and names before any prompt leaves your VPC. It’s not glamorous. It is effective. Log what got redacted, so you can prove a control fired. Then reduce your exposure surface: opt out of vendor training, rotate keys, and restrict privileges.
This can go live fast. You don’t need a 90‑day project to implement basics. You need a small set of regexes, an allowlist, and a CI step. Then you harden. If you’re already moving content through a system like Oleno, you can layer redaction ahead of job execution without changing how your team writes.
Pair these quick wins with vendor settings that match your risk posture. A short retention window, IP allowlists, and per‑job keys go a long way to containing blast radius.
The Root Cause Is Unmapped Data Paths, Not The Model
Data leaks rarely come from the model itself. They come from unmapped paths where data enters, moves, and gets stored. Map your sensitive fields. Redact at the edge. Scope retrieval narrowly. Then set vendor policies in both contracts and configuration. Finally, ask for proof that those settings actually hold.

Map Sensitive Fields And Write Redaction Rules Close To The Input
If you can’t name sensitive fields, you can’t protect them. Start with a field map for PII, IP, and business-sensitive data. Think beyond obvious. It’s not just emails and SSNs. It’s customer names in briefs, CRM snippets in retrieval chunks, and export IDs in metadata that ride along unnoticed.
Write redaction rules where data first enters the pipeline. Combine regex patterns with allowlists for approved entities. Test using seeded examples before going live. It’s boring work. It’s also how you build trust. In my small-team days, we had no time for rework. Front-loading controls would have saved us a dozen messy cycles.
Your goal isn’t perfect detection. It’s layered defense. Redact at ingress, validate post-redaction payloads, and snapshot masked prompts for audits. If a rule fails, block the job. Don’t warn. Don’t “allow once.”
Scope Retrieval, Add Claim Filters, Enforce Provenance-First Citations
Scope queries to a low-risk namespace. Pull only from approved, citation-ready documents. Add claim filters that require each statement to map to a source. Return citations before prose. This order matters. Evidence first keeps drafts on-rails, and legal reviews shorter.
Use chunk-level IDs and signed URLs, so every sentence maps back to something verifiable. Reviewers shouldn’t hunt. They should click. Tools that align with AI data security practices emphasize this kind of provenance. You’ll feel the difference when someone asks, “Where did this come from?” and you answer in one second.
Run adversarial tests. Ask for information you know is out of scope. Make sure the system declines with a cited reason. That’s control you can demonstrate.
How Do You Keep Vendors From Training On Your Data?
Two moves. Contract and configuration. In contracts, require a DPA, no training on your prompts, transparent subprocessors, deletion timelines, and data residency options. In configuration, disable training, set short retention, use per‑job keys, and IP‑allowlist calls.
Then verify. Don’t trust. Ask for attestation. Schedule periodic reviews. Guidance like Microsoft’s DSPM for AI frames this as ongoing posture management, not a one-time checklist. Your controls should be inspectable on demand. Prefer proof over promises.
Tie vendor configs to environment variables and deployment. If you migrate or scale, your guardrails should come with you automatically.
The Hidden Cost Of PII And Compliance Failures
PII leaks create more than embarrassment. They create rework, legal reviews, and engineering thrash. Every hour you spend on takedowns and incident docs is an hour not spent shipping. Compliance isn’t paperwork. It’s cycle time. Miss a checkbox and your release sits, while momentum bleeds.
Let’s Pretend You Ship A Draft With An Email In The Prompt
Let’s pretend a prompt included a customer email, and that detail survived redaction. One blog goes live. It’s mirrored to socials and the newsletter. Now you’re managing takedowns and drafting a disclosure. You didn’t just lose time. You created a discoverable incident that burns trust and budget.
You’ll loop legal, redact archives, and re-run the piece. Then you’ll patch your process under stress. This is a bad way to learn. Articles on handling sensitive content in regulated industries, like this Thomson Reuters overview for law firms, emphasize prevention because cleanup is expensive.
You’re not avoiding work by skipping controls. You’re deferring it into a crisis.
The Compliance Tax: Retention, Residency, And Subprocessors
Regulations won’t slow down for your calendar. You need documented retention settings, residency alignment, and a current list of subprocessors that touch prompts, logs, and vector stores. If those live in a side doc, they’re already out of date. Bake them into the release process, not a separate checklist.
Each missing detail adds legal review loops. That delays publishing and forces context switching. A small team can’t absorb that tax for long. External primers like this DataGuard summary on AI privacy concerns are helpful for scope, but the real unlock is operationalizing the checks in your pipeline.
Your secure path should be the fastest path. Anything else will be bypassed under pressure.
Engineering Time Sink From Break-Fix Privacy Work
Reactive privacy ops is an engineering tax. You’ll debug webhook payloads after a scare, rotate keys late, and rewrite redaction rules after an edge case. Each incident spawns more ad hoc tasks. It’s costly. It’s demoralizing.
Put tests around prompts and payloads. Add contract tests for vendors. Use idempotent publishing with strict retry behavior to avoid replaying sensitive events. Every safeguard you encode reduces late-night firefighting. I’ve watched teams spend weeks unraveling avoidable mistakes. The fix isn’t heroics. It’s structure.
If this sounds familiar, it’s time to change the system, not the people. Still untangling manual reviews? There’s a faster route to consistent output. Try using an autonomous content engine for always-on publishing.
The Moment You Realize A Draft Leaked Something It Should Not
When legal calls, your process changes overnight. Throughput drops, confidence dips, and every publish feels like a special case. You don’t fix this with more meetings. You fix it with controls that make leaks unlikely and proof that’s easy to show. Make the safe path the default path.
When Legal Calls After Publish
That call shifts a team’s posture. Anxiety goes up. Managers start to hover. Reviews multiply. The creative work slows because no one trusts the system. You need a plan that doesn’t require heroics. You need artifacts, not opinions.
Show redaction logs, prompt snapshots, and vendor settings in one place. If you can surface evidence in minutes, you shorten the conversation. Enterprise content teams that formalize this—see discussions like OpenText’s secure AI content management overview—move faster precisely because they can prove control.
Proof calms everyone down. That’s worth more than another meeting.
Your Writer At 3 AM, Worried About A Leak
People remember the scary nights. A DM about a possible leak. A “can you pull this?” request. Your writer’s confidence matters. Give them clarity. If they know the system redacts at ingress, stores a masked prompt snapshot, and scopes retrieval safely, they sleep. If they don’t, they hesitate.
Clear coverage beats tribal knowledge. You can’t promise perfection. You can promise that the checks run the same way, every time, and that you’ll catch most issues before publish. That builds trust with the team, not just with legal.
Confidence isn’t fluff. It’s a function of reliability.
Why Leaders Lose Confidence Without Audit Trails
Executives don’t need a lecture. They need proof. Show redaction logs, retrieval scopes, vendor configurations, and retention evidence. Bundle it. Make incident drills part of your cadence, so it’s routine, not a scramble.
“Trust us” is not a plan. A brief primer like Clinked’s take on protecting customer data with AI is fine for context. But leaders want your evidence, not someone else’s blog. Build the dashboard. Make it boring.
Do that, and approvals speed up. Don’t, and every release drags.
A Practitioner Framework For Secure AI Integrations In Content Ops
A secure AI content pipeline starts with classification and redaction at ingress, retrieval scoped to approved sources, and citations before prose. Then you lock down storage and access. Finally, you operationalize observability and incident response. These are small moves, but they compound into a safer, faster path.
Classify Inputs And Automate Redaction End To End
Define a minimal set of sensitive fields. Start simple: emails, phones, IDs, names, customer handles. Treat anything customer-derived as suspect by default. That’s your baseline. You can expand later with context-aware rules.
Automate redaction at ingress. Use regex for obvious patterns and allowlists for approved terms. If you need it, add an ML scrubber for context-bound entities, but only after you’ve proven the basics. Validate that redaction occurred, snapshot the masked prompt, and block the job if checks fail. Don’t rely on a manual checklist.
Seed test data in staging. Force failures. Your goal is predictable behavior, not cleverness. You’ll move faster once you know the guardrails are actually there.
Design Prompt-Safe Retrieval With Claim Guards And Citations
Scope queries to a safe namespace. Only approved, citation-friendly sources make the cut. Add claim guards that reject un-cited statements. Return citations first, then assemble the answer. That pattern keeps drafts grounded and reviews short.
Every chunk should carry provenance metadata. Reviewers click back to source, not guess. Use adversarial prompts to verify leakage controls. Make the system say “no” when it should. Approaches aligned with provenance-first drafting aren’t academic; they’re how small teams keep quality up while volume increases.
If a claim can’t be sourced, the draft should tell you that explicitly. No source, no sentence.
Configure Vector Stores And Hosting For Encryption And Access Control
Pick a vector database with encryption at rest and KMS support. Use per‑environment API keys and short‑lived credentials. Limit indexes by job, not by team or department. Keep blast radius small.
If residency or data-sharing constraints apply, consider VPC-hosted or on-prem models. Measure the latency trade-offs. Document the decision, and revisit as your workloads shift. The hosting choice isn’t forever. It’s a posture that evolves with your risk and performance needs.
Keep configs in code. Drift is the enemy. If your infrastructure scales, your controls should scale with it automatically.
Operationalize Observability, Audits, And Incident Playbooks
Log redactions, retrieval scopes, citations, and publishing events. Set retention policies. Anonymize logs where possible. Add alerts for risky terms and unusual retrieval scopes. This isn’t surveillance. It’s how you spot problems early.
Drill incident workflows quarterly. Include rollback and disclosure steps. Define who approves what, and under which conditions. Keep the plan where people work, not buried in a policy binder. Industry guidance like Publicis Sapient’s data security for AI overview points to the same truth: process beats promises.
Your best metric is boring outcomes. Systems that run quietly tend to be configured well.
How Oleno Implements Privacy-First AI Content Ops
Oleno helps small teams run demand generation with predictable quality and fewer leaks by enforcing rules, grounding claims, and controlling publishing. You define what’s true, what’s allowed, and how you sound. Oleno turns that into deterministic execution with QA gates, so the safe path becomes the fastest path.
Governed Knowledge And Claim Control Reduce Prompt Risk
You encode product truth, approved claims, and language rules once. Oleno applies those rules everywhere, so outputs stay inside guardrails. That alone reduces the chance sensitive context is pulled into a prompt or a draft wanders into unsourced territory. It also makes reviews simpler and faster.


Knowledge-base grounding keeps drafts tethered to your real materials. Claim control rejects statements that don’t align with approved sources. You still manage encryption and vendor settings in your stack. That’s by design. Strategy and risk posture remain yours. Oleno makes adherence operational, not aspirational.
If you’ve struggled with drift as volume increases, this is the lever that brings it back in line.
Deterministic Pipelines With QA Gates And Role-Based Approvals
Oleno runs a repeatable pipeline. The same checks fire the same way, every time. Voice, narrative, grounding, and accuracy gates block publishing until they pass. That predictability reduces rework and eliminates “did we check that?” moments.
You can align these gates to how your team approves work. Legal can review high‑risk jobs without slowing everyday publishing. That’s the balance small teams need: oversight where it matters, momentum where it doesn’t. When priorities shift, the system keeps running because the rules don’t live in someone’s head.
In practice, this looks like fewer late surprises and shorter review cycles. You feel it in the calendar.
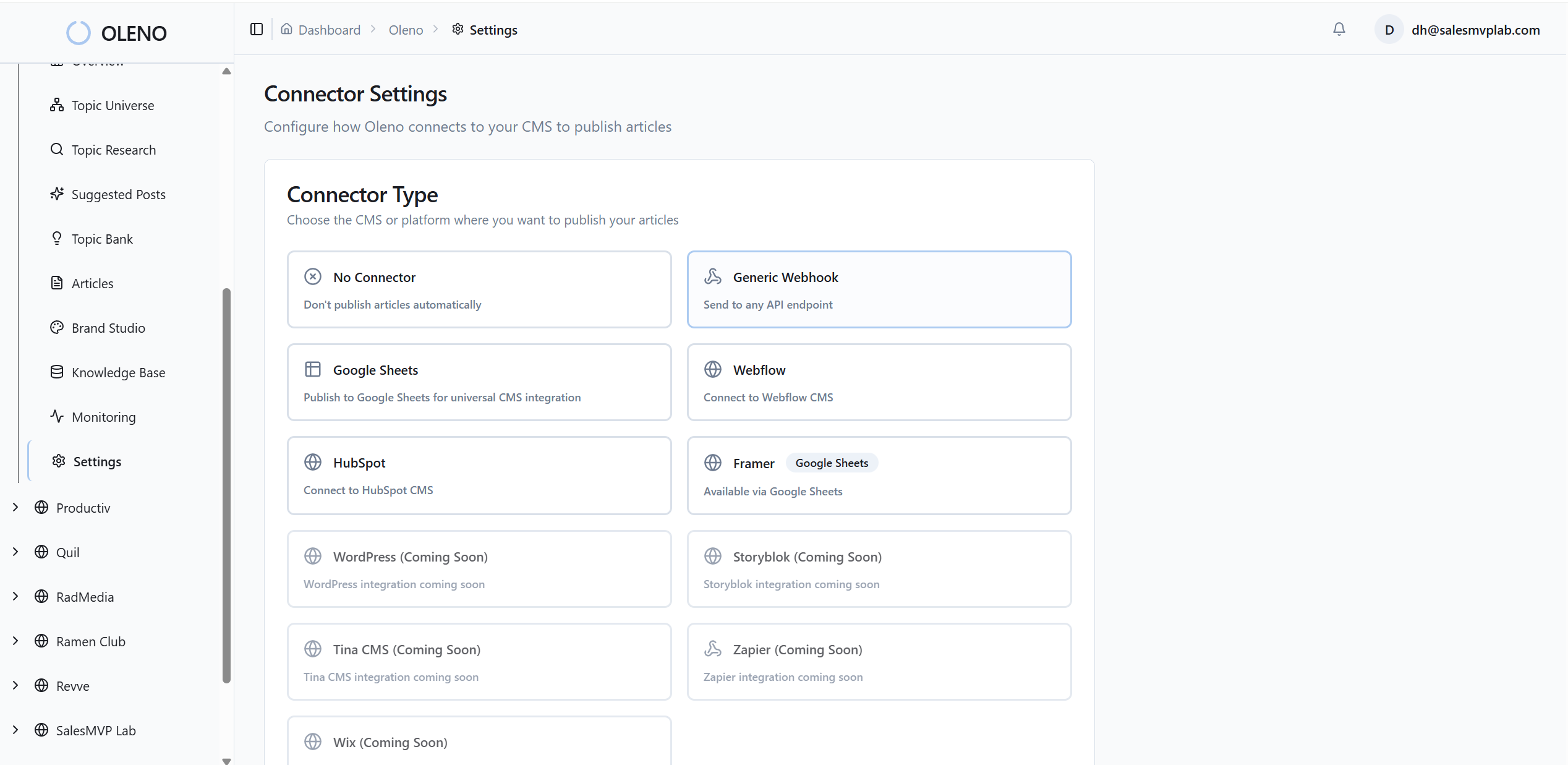
CMS Publishing With Webhooks, Idempotency, And Logs
Publishing shouldn’t create risk. Oleno publishes directly to your CMS and avoids duplicates through idempotent behavior. Draft or live. Your call. If a publish fails, the system handles it predictably, so you don’t end up with half-published content.
Pair Oleno’s publishing control with your environment’s webhooks and logs. Keep redaction artifacts and prompt snapshots alongside version history in your stack, so rollbacks are quick and evidence is ready. This keeps the audit trail tight and your operations calm under pressure.
Want to validate this flow on low-risk content first? Run a short pilot and measure the reduction in rework. Try Oleno for free.
Conclusion
Secure AI in content ops isn’t a feature. It’s a set of boring, reliable controls that run every time: redact at ingress, retrieve from safe scopes, cite first, publish predictably, and keep proof on hand. Do that, and leaks get unlikely, reviews speed up, and your team ships with less stress. That’s the real win: safety that makes you faster.
About Daniel Hebert
I'm the founder of Oleno, SalesMVP Lab, and yourLumira. Been working in B2B SaaS in both sales and marketing leadership for 13+ years. I specialize in building revenue engines from the ground up. Over the years, I've codified writing frameworks, which are now powering Oleno.
Frequently Asked Questions